ROUTER COMMANDS
Sunday, February 1, 2009ROUTER COMMANDS
TERMINAL CONTROLS:
· Config# terminal editing - allows for enhanced editing commands
· Config# terminal monitor - shows output on telnet session
· Config# terminal ip netmask-format hexadecimal|bit-count|decimal - changes the format of subnet masks
HOST NAME:
· Config# hostname ROUTER_NAME
BANNER:
· Config# banner motd # TYPE MESSAGE HERE # - # can be substituted for any character, must start and finish the message
VPN [Cisco Router - PPTP Server] from oprekan.wordpress.com
Monday, November 3, 20081. Configure VPDN untuk dial in VPN dari Microsoft VPN Client
RO-PPTP(config)# vpdn enable
RO-PPTP(config)# vpdn-group PPTP-DIALIN
RO-PPTP(config-vpdn)# accept-dialin
RO-PPTP(config-vpdn)# protocol pptp
RO-PPTP(config-vpdn)# virtual-template 1
RO-PPTP(config-vpdn)# exit
2. Aktifkan interface untuk IP Dial In di Microsoft VPN Client dan LAN yang
akan kita akses dari luar leat VPN ini.
RO-PPTP(config)# interface Ethernet5/0
RO-PPTP(config-if)# description DIAL-IN IP INTERFACE FROM OUTSIDE
RO-PPTP(config-if)# ip address 202.150.64.81 255.255.255.240
RO-PPTP(config-if)# no shutdown
RO-PPTP(config)# interface Ethernet5/1
RO-PPTP(config-if)# description SECURED-LAN
RO-PPTP(config-if)# ip address 192.168.0.254 255.255.255.0
RO-PPTP(config-if)# no shutdown
3. Create Virtual-template untuk sebagai virtual interface untuk diapply ke inbound VPN connections.
IP menggunakan unnunmbered E5/1 agar nantinya IP yang didapat oleh
Microsoft VPN client dalam satu subnet dengan IP Secured-LAN.
IP client diperoleh dari DHCP dari Pool Address pptp-pool (misalnya)
RO-PPTP(config)# interface Virtual-Template1
RO-PPTP(config-if)# ip unnumbered ethernet5/1
RO-PPTP(config-if)# peer default ip address pool pptp-pool
RO-PPTP(config-if)# ppp encrypt mppe auto required
(Bila Router Anda tidak support, lewatkan saja & di Micorosoft VPN client dibagian security, Require Data Encryptionnya tidak usah di check-list / centang).
RO-PPTP(config-if)# ppp authentication ms-chap ms-chap-v2 chap pap
(enable semua bila perlu chap/pap selain Microsoft)
4. Create Pool IP Address untuk VPN ‘pptp-pool’ (misal untuk 20 user / ip) & pastikan IP pool tersebut tidak dipakai di Secured-LAN
RO-PPTP(config)# ip local pool pptp-pool 192.168.0.100 192.168.0.119
5. Create Account untuk login VPN
RO-PPTP(config)# username vpdn password 0 pptp
6. Configure Autentikasi PPP vpn ini ke local (Router) atau selanjutnya ke Radius bila memang sudah available.
RO-PPTP(config)# aaa new-model
RO-PPTP(config)# aaa authentication ppp default local
Berikut Konfigurasi Lengkap (hanya vpdn saja) :
================================================
username vpdn password 0 pptp
!
aaa new-model
aaa authentication ppp default local
!
vpdn enable
!
vpdn-group PPTP-DIALIN
accept-dialin
protocol pptp
virtual-template 1
!
interface Ethernet5/0
description DIAL-IN IP INTERFACE FROM OUTSIDE
ip address 202.150.64.81 255.255.255.240
!
interface Ethernet5/1
description SECURED-LAN
ip address 192.168.0.254 255.255.255.0
!
interface Virtual-Template1
ip unnumbered Ethernet0/1
peer default ip address pool pptp-pool
ppp encrypt mppe auto required
ppp authentication ms-chap ms-chap-v2 chap pap
!
ip local pool defaultpool 192.168.0.100 192.168.0.119
================================================
ACCESS LIST (ACL)
Saturday, November 1, 2008Pengertian
- Jaringan traffic flow dan pengaruh desain keamanan manajemen jaringan computer.
- Access lists mengijinkan atau menolak pernyataan bahwa filter traffic dapat ke segmen jaringan dan dari segmen jaringan berdasarkan pada:
- Alamat sumber
- Alamat tujuan
- Tipe protocol
- Dan nomor port dari paket.
Access list adalah pengelompokan paket berdasarkan kategori. Access list bisa sangat membantu ketika membutuhkan pengontrolan dalam lalu lintas network. access list menjadi tool pilihan untuk pengambilan keputusan pada situasi ini.
Penggunaan access list yang paling umum dan paling mudah untuk dimengerti adalah penyaringan paket yang tidak diinginkan ketika mengimplementasikan kebijakan keamanan.
Sebagai contoh kita dapat mengatur access list untuk membuat keputusan yang sangat spesifik tentang peraturan pola lalu lintas sehingga access list hanya memperbolehkan host tertentu mengakses sumber daya WWW sementara yang lainnya ditolak. Dengan kombinasi access list yang benar, network manajer mempunyai kekuasaan untuk memaksa hamper semua kebijakan keamananyang bisa mereka ciptakan.
Access list juga bisa digunakan pada situasi lain yang tidak harus meliputi penolakan paket. Sebagai contoh access list digunakan untuk mengontrol network mana yang akan atau tidak dinyatakan oleh protocol dynamic routing. Konfigurasikan access list dengan cara yang sama. Perbedaannya disibni hanyalah bagaimana menerapkannya ke protocol routing dan bukan ke interface. Kita juga bisa menggunakan access list untuk mngkategorikan pakt atau antrian /layanan QOS, dan mengontrol tipe lalu lintas data nama yang akan mengaktifkan link ISDN.
Membuat access list sangat mirip dengan statement pada programming if – then jika sebuah kondisi terpenuhi maka aksi yang diberikan akan dijalankantidak terpenuhi, tidak ada yang terjadi dan statemen berikutnya akan dievaluasi. Statement ACL pada dasarnaya dalah paket filter dimana paket dibandingkan, dimana paket dikategorikan dan dimana suatu tindakan terhadap paket dilakukan.
List(daftar) yang telah dibuat bisa diterpakan baik kepada lalulintas inbound maupun outbound pada interface mana saja. Menerapkan ACL menyebabkan router menganalisa setiap paket arah spesifik yang melalui interface tersebut dan mengmbil tindakan yang sesuai.
Ketika paket dibandingkan dengan ACL, terdapat beberapa peraturan (rule) penting yang diikuti:
- Paket selalu dibandingkan dengan setiap baris dari ACL secara berurutan, sebagai contoh paket dibandingkan dengan baris pertama dari ACL, kemudian baris kedua, ketiga, dan seterusnya.
- Paket hanya dibandingkan baris-baris ACL sampai terjadi kecocokan. Ketika paket cocok dengan kondisi pada baris ACL, paket akan ditindaklanjuti dan tidak ada lagi kelanjutan perbandingan.
- Terdapat statement “tolak” yang tersembunyi (impilicit deny) pada setiap akhir baris ACL, ini artinya bila suatu paket tidak cocok dengan semua baris kondisi pada ACL, paket tersebut akan ditolak

Jenis ACL
- Standard ACL
Standard ACL hanya menggunakan alamat sumber IP di dalam paket IP sebagai kondisi yang ditest. Semua keputusan dibuat berdasarkan alamat IP sumber. Ini artinya, standard ACL pada dasarnya melewatkan atau menolak seluruh paket protocol. ACL ini tidak membedakan tipe dari lalu lintas IP seperti WWW, telnet, UDP, DSP.
- Extended ACL
Extended ACL bisa mengevalusai banyak field lain pada header layer 3 dan layer 4 pada paket IP. ACL ini bisa mengevaluasi alamat IP sumber dan tujuan, field protocol pada header network layer dan nomor port pada header transport layer. Ini memberikan extended ACL kemampuan untuk membuat keputusan-keputusan lebih spesifik ketika mengontrol lalu lintas.
Jenis Lalu Lintas ACL
- Inbound ACL
Ketika sebauah ACL diterapkan pada paket inbound di sebuah interface, paket tersebut diproses melalui ACL sebelum di-route ke outbound interface. Setiap paket yang ditolak tidak bisa di-route karena paket ini diabaikan sebelum proses routing diabaikan.
- Outbond ACL
Ketika sebuah ACL diterapkan pada paket outbound pada sebuah interface, paket tersebut di-route ke outbound interface dan diproses melalui ACL malalui antrian.
Panduan Umum ACL
Terdapat beberapa panduan umum ACL yang seharusnya diikuti ketika membuat dan mengimplementasikan ACL pada router :
- Hanya bisa menerapkan satu ACL untuk setiap interface, setiap protocol dan setiap arah. Artinya bahwa ketika membuat ACL IP, hanya bisa membuat sebuah inbound ACL dan satu Outbound ACL untuk setiap interface.
- Organisasikan ACL sehingga test yang lebih spesifik diletakkan pada bagian atas ACL
- Setiap kali terjadi penambahan entry baru pada ACL, entry tersebut akan diletakkan pada bagian bawah ACL. Sangat disarankan menggunakan text editor dalam menggunakan ACL
- Tidak bisa membuang satu baris dari ACL. Jika kita mencoba demikian, kita akan membuang seluruh ACL. Sangat baik untuk mengcopy ACL ke text editor sebelum mencoba mengubah list tersebut.
- Wildcard Masking
Wildcard masking digunakan bersama ACL untuk menentukan host tunggal, sebuah jaringan atau range tertentu dari sebuah atau banyak network. Untuk mengerti tentang wildcard, kita perlu mengerti tentang blok size yang digunkan untuk menentukan range alamat. Beberapa blok size yang berbeda adalah 4, 8, 16, 32, 64.
Ketika kita perlu menentukan range alamat, kita memilih blok size selanjutnya yang terbesar sesuai kebutuhan. Sebagai contoh, jika kita perlu menentukan 34 network, kita memerlukan blok size 64. jika kita ingin menentukan 18 host, kita memerlukan blok size 32. jiak kita perlu menunjuk 2 network, maka blok size 4 bisa digunakan. Wildcard digunakan dengan alamat host atau network untuk memberitahukan kepada router untuk difilter.
Untuk menentukan sebuah host, alamat akan tampak seperti berikut 172.16.30.5 0.0.0.0 keempat 0 mewakili setiap oktet pada alamat. Dimanapun terdapat 0, artinya oktet pada alamat tersebut harus persis sama. Untuk menentukan bahwa sebuah oktet bisa bernilai apa saja, angka yang digunakan adalah 255. sebagai contoh, berikut ini adalah subnet /24 dispesifikasikan dengan wildcard: 172.16.30.0 0.0.255 ini memberitahukan pada router untuk menentukan 3 oktet secara tepat, tapi oktet ke-4 bisa bernilai apa saja.
Standard Access List
Standard IP ACL memfilter lalu lintas network dengan menguji alamat sumber IP didalam paket. Kita membuat standard IP ACL dengan menggunakan nomor ACL 1-99 atau 1300-1999(expanded range).Tipe ACL pada ummnya dibedakan berdasarkan nomor yang digunakan ketika ACL dibuat, router akan mengetahui tipe syntax yang diharapkan untuk memesukkan daftar.
Dengan menggunakan nomor 1-99 atau 1300-1999, kita memberitahukan kepada router bahwa kita ingin membuat IPACL, jadi router akan mengharapkan syntax yang hana menspesifikasikan alamat sumber IP pada baris pengujian.
Banyak range nomor ACL pada contoh dibawah ini yang bisa kita gunakan untuk memfilter lalu lintas pada jaringan kita (protocol yang bisa kita terapkan ACL bisa tergantung pada versi IOS kita) :
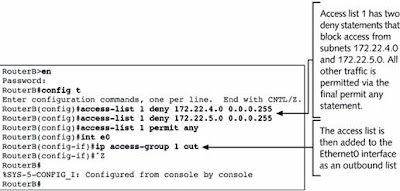
Contoh Standard ACL
Standard ACL untuk menghentikan user tertentu mendapatkan akses ke LAN Department Finance.
Pada gambar, router mempunyai 3 koneksi LAN dan 1 koneksi WAN ke internet. User pada LAN Sales tidak boleh mempunyai akses ke LAN finance, tapi mereka boleh mengakses internet dan Department Marketing.
LAN Marketing perlu mengakses LAN Finance untuk layanan aplikasi
Pada router yang digambar, standard IP ACL berikut dikonfigurasi :
Lab_A#config t
Lab_A(config)#access -list 10 deny 172.16.40.0 0.0.0.255
Lab_A(config)#access-list 10 permit any
Sangatlah penting untuk diketahui bahwa perintah any sama halnya dengan menggunakan wildcard masking berikut :
Lab_A(config)#access-list 10 permit 0.0.0.0 255.255.255.255
Karena wildcard mask menyatakan bahwa tidak ada oktet yang diperiksa, setiap alamat akan sesuai dengan kondisi test. Jadi fungsi ini sama dengan penggunaan kata any. Saat ini, ACL dikonfigurasi untuk menolak alamat sumber dari LAN sales yang mengakses LAN finance, dan memperbolehkan dari akses yang lain. Tetapi untuk diingat, tidak ada tindakan yang diambil sampai akses list diterapkan pada arah yang spesifik. Tetapi dimana ACL ini seharusnya ditempatkan? Jika kita menempatkannya pada E0, kita mungkin akan mematikan juga interface Ethernet karena semua peralatan LAN Sales akan ditolak akses ke semua network yang terhubung ke router.
Tempat terbaik untuk menerapkan ACL ini adalah pada E1 sebagai outbound list:
Lab_A(config)#Int E1
Lab_A(config-if)#ip access-group 10 out
Ini menghentikan secara tuntas lalu lintas 172.16.40.0 keluar dari Ethernet 1. Ini tidak ada pengarujnya terhadap host dari LAN Sales yang mengakses LAN marketing dan internet, karena lalu lintas ke tujuan tersebut tidak melalui interface E1. Setiap paket yang mencoba keluar dari E1 harus melalui ACL terlebih dahulu. JIka terdapat inbound lit yang ditempatkan pada E0, maka setiap paket yang mancoba masuk ke interface E0 akan harus melalui ACL terlebih dahulu sebelum di route ke interface keluar.
Keistimewaan Standard Access List
Software Cisco IOS dapat memprovide pesan logging tentang paket – paket. Yang diijinkan atau ditolak oleh standard IP access list. Itulah sebabnya beberapa paket dapat cocok dengan access list.yang disebabkan oleh informasi pesan logging.tentang paket yang telah dikirimkan ke console. Level dari pesan logging ke console yang dikendalikan oleh perintah logging console.Kemampuan ini hanya terdapet pada extended IP access lists.
Triggers paket pertama access list menyebabkan logging message yang benar, dan paket – paket berikutnya yang dikunpulkan lebih dari interval 5-menit sebelum ditampilkan. Pesan logging meliputi nomor access list, apakah paket tersebut diterima atau ditolak, alamat IP sumber dari paket dan nomor asal paket yang diterima sumber atau ditolak dalam interval 5 menit.
KEUNTUNGAN
Kita dapat memantau berapa banyak paket yang diijinkan atau ditolak oleh access list khusus termasuk alamat tujuan setiap paket.
Membuat Standard Access List Menggunakan Nomor
Untuk membuat nomor standard access list dan menerima pesan logging, ditampilkan dalam mode global konfigurasi, sebagai berikut :
Membuat Standard Access List Menggunakan Nama
Untuk membuat nama standard access list dan menerima pesan logging, berikut adalah permulaan dalam mode global konfigurasi.
Untuk mendefinisikan standard IP access list dengan nomor, menggunakan standard version dari acess-list ration untuk memindahkan sebuah standard access list, maka digunakan perintah berikut :
access-list access-list-number {deny permit} source [source-wildcard] [log] no access-list access-list-number
Extended ACL
Extended ACL bisa mengevaluasi banyak field lain pada header layer 3 dan layer 4 pada paket IP. ACL ini bisa mengevaluasi IP sumber dan tujuan, field protocol dalam network header Network Layer dan nomor port pada Transport Layer. Ini memberikan extended ACL kemampuan untuk membuat keputusan – keputusan lebih spesifik ketika mengontrol lalu lintas.
Pada contoh Standard ACL, perhatikan bagaimana kita harus memblok semua akses dari LAN Sales ke Department Finance. Bagaimana jika untuk urusan keamanan, kita membutuhkan Sales mendapatkan akses ke server tertentu pada LAN Finance tapi tidak ke layanan network lainnya ? Dengan standard IP ACl, kita tidak memperbolehkan user mendapat satu layanan sementara tidak untuk yang lainnya. Dengan kata lain, ketika kita membutuhkan membuat keputusan berdasarkan alamat sumber dan tujuan, standard ACL tidak memperbolehkan kita melakukannya karena ACL ini hanya mambuta kaputusan berdasrkan alamat sumber. Tetapi extended ACl akan membantu kita karena extended ACL memperbolehkan kita menentukan alamat sumber dan tujuan serta protocol dan nomor port yang mengidentfikasikan protocol upper layer atau aplikasi. Dengan menggunakan extended ACL kita bisa secara efisien memperbolehkan user mengakses ke fisik LAN dan menghentikan host tertentu atau bahkan layanan tertentu pada host tertentu.
Contoh Extended Access List
Layanan lain pada host ini dan host lainnya bisa diakses oleh departertmen seles dan marketing. Berikut adalah access list yang dibuat:
Lab_A#config t
Lab_A(config)#access-list 110 deny tcp any host 172.16.30.5 eq 21
Lab_A(config)#access-list 110 deny tcp any host 172.16.30.5 eq 23
Lab_A(config)#access-list 110 permit ip any any
Access list 110 memberitahukan ke router bahwa anda membuat Extended IP Access List. TCP adalah field procol pada heather layer network. Jika pada list tidak terdapat TCP disini, anda tidak bisa menyaring berdasarkan nomor port 21 dan 23 seperti yang diperlihatkan pada contoh (yaitu FTP dan Telnet dan keduanya menggunakan TCP untuk layanan conection - oriented). Perintah any disini adalah sumber, yang berarti semua alamat IP dan host adalah alamat IP tujuan. Setelah list dibuat, maka selanjutnya perlu diterapkan pada outbound interface ethernet 1.
- Hukum Access List
- Daftar aplikasi router secara berurutan menunjukan apa yang ditulis ke daalm router.
- Daftar aplikasi router untuk paket yang berurutan.
- Packet akan diproses jika cocok dan berdasarkan criteria access list termasuk pernyataan access list.
- Implicit deny any
- Semua paket yang tidak memenuhi syarat dari acces list akan di blok oleh perintah permit any yang digunakan pada akhir list.
- Hanya satu list, per protocol, per perintah yang dapat diaplikasikan pada interface.
- Kita tidak dapat memindahkan satu baris dari access list.
- Access list akan efektif segera setelah diaplikasikan.
Deskripsi Syntax
Beberapa bentuk fungsi access Lists dengan cisco router, meliputi
- Implementasi keamanan prosedur access
- Seperti [ada protocol firewall
PPP with CHAP Authentication
PPP with CHAP Authentication
PPP (Point-to-Point Protocol)
PPP (Point-to-Point Protocol) is a protocol for communication between two computers using a serial interface, typically a personal computer connected by phone line to a server. For example, your Internet server provider may provide you with a PPP connection so that the provider's server can respond to your requests, pass them on to the Internet, and forward your requested Internet responses back to you. PPP uses the Internet protocol (IP) (and is designed to handle others). It is sometimes considered a member of the TCP/IP suite of protocols. Relative to the Open Systems Interconnection (OSI) reference model, PPP provides layer 2 (data-link layer) service. Essentially, it packages your computer's TCP/IP packets and forwards them to the server where they can actually be put on the Internet.
PPP is a full-duplex protocol that can be used on various physical media, including twisted pair or fiber optic lines or satellite transmission. It uses a variation of High Speed Data Link Control (HDLC) for packet encapsulation.
PPP is usually preferred over the earlier de facto standard Serial Line Internet Protocol (SLIP) because it can handle synchronous as well as asynchronous communication. PPP can share a line with other users and it has error detection that SLIP lacks. Where a choice is possible, PPP is preferred.
CHAP (Challenge-Handshake Authentication Protocol)
CHAP (Challenge-Handshake Authentication Protocol) is a more secure procedure for connecting to a system than the Password Authentication Procedure (PAP). Here's how CHAP works:
After the link is made, the server sends a challenge message to the connection requestor. The requestor responds with a value obtained by using a one-way hash function.
The server checks the response by comparing it its own calculation of the expected hash value.
If the values match, the authentication is acknowledged; otherwise the connection is usually terminated.
At any time, the server can request the connected party to send a new challenge message. Because CHAP identifiers are changed frequently and because authentication can be requested by the server at any time, CHAP provides more security than PAP. RFC1334 defines both CHAP and PAP.
Configuring PPP w/CHAP on a Cisco Router
The interface command to enable ppp is:
encapsulation ppp
Place this on both ends and that is it. However, to enable authentication, we need to add the interface command
ppp authentication chap
to both routers, the routers will now require authentication over the link. They will attempt to log in with their HOSTNAME as their USERNAME and their ENABLE password as their chap PASSWORD. We must create an entry in the router that matches the remote routers username and password (global config):
username Other_Router password Other_enable_pass
That is all their is to basic PPP.
Our Samples:
(R1)s0----------s0(R2)
PPP Without CHAP
Router 1:
hostname R1
interface serial 0
encapsulation PPP
no shutdown
Router 2:
hostname R2
interface serial 0
encapsulation PPP
no shutdown
PPP With CHAP default names and password
Router 1:
hostname R1
enable secret toast1
username R2 password cool2
interface serial 0
encapsulation PPP
ppp authentication chap
no shutdown
Router 2:
hostname R2
enable secret cool2
username R1 password toast1
interface serial 0
encapsulation PPP
ppp authentication chap
no shutdown
Copyright (c) 2001 Boson Software, Inc. All Rights Reserv
Interior Gateway Routing Protocol (IGRP)
P Addresses: Please set these IP addresses on the interfaces of your routers.
Router1 Router2 Router4
Interface Ethernet 0 10.1.1.1 255.255.255.0 10.1.1.2 255.255.255.0 Not Available
Interface Serial 0 172.16.10.1 255.255.0.0 Not Available 172.16.10.2 255.255.0.0
Lets connect to Router1 and get it configured. We will be using the table above for our IP addresses.
IGRP is classful, meaning it does not include the subnet mask in its routing table updates. So now lets go ahead and start the lab.
1. We first want to configure Router1 for IGRP. To enable IGRP as the routing protocol we only need to type: router IGRP AS. The AS stands for a Autonomous System number. An Autonomous System is defined as a network under a common administration with a common routing policy. You will need to use the SAME autonomous system number on every router that you would like to share its routing table with. We can see this below in the router output. Notice the new mode we have entered
Router1(config)#router IGRP 100
Now that we have IGRP running on our Router we need to tell the router which networks it is connected to. We do this by using the network statement. What this means is every interface of our router that is directly connected to an active network needs a network number. We will have some networks using the same ip addressing schemes with different subnets, and some are using entirely different addressing schemes. Look at the diagram below. In this diagram we have three different kinds of addressing schemes. Lets look at these in more detail. On Router 1 we have an IP address of 10.1.1.1 with a /24 subnet mask. Since IGRP is classful you are only required to enter the class part of the address for the network statement. For example on Router1 we have already issued the command router IGRP, we then need to specify the directly connected networks to Router1 so the router can advertise these routes in its routing table. To do this we would only need to type: network 10.0.0.0 now we have not told the router about the network on his serial interface, to do this we would type: network 172.16.0.0 Lets look at Router 2 what network statement would we need to use on this router ______________________________________(see the answer below the diagram.)
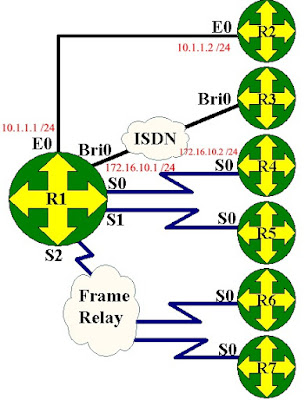
The answer is network 10.0.0.0. The network statement for the ethernet link is the same for Router1 and Router2. On router1 what network statement would you need for the serial link? For this network statement you used the classful portion of the address 172.16.10.1 which would be just network 172.16.0.0.
Now that we understand the network command lets enter it on our Router1.
Router1(config-router)#network 172.16.0.0
If you notice we only needed to enter 10.0.0.0 for our network statement, this is because 10.0.0.0 is a Class B address and IGRP only uses the classful portion of the address. Now we have configured Router1 for IGRP lets connect to Router2 and get it setup.
We need to connect to Router2 and follow the same instructions. Lets select Router2 from the Window pull down menu. When we connect we are going to set a hostname to Router2, then set the ip addresses to the table above and configure IGRP.
Router>en
Now add the IGRP stuff!
Router2(config)#router IGRP 100
We should now have IGRP running on our network between Router1 and Router2. We need to get Router4 setup.
We need to connect to Router4 and follow the same instructions. Lets select Router4 from the Window pull down menu. When we connect we are going to set a hostname to Router4, then set the ip addresses to the table above and configure IGRP.
Router>en
Now add the IGRP stuff!
Router4(config)#router IGRP 100
Now that we have IGRP running on our entire network lets verify that it is receiving routes. To do this we will be using some show commands. The most common one is show ip route. This displays all entries in the routing table. If we do this on our Router B we will see the route to our directly connected Router1. Lets take a look at our routing table, to do this type: show ip route from the privilege mode.
Lets look at the first entry I 10.1.1.0/24 [100/1] via 172.16.10.2, 00:00:21, Serial0. It starts off with I this says it is a IGRP route it then says the destination network with sunbet mask in this case it is 10.1.1.0 with a /24 (255.255.255.0) subnet mask. Next it gives 100/1 the 100 is the administrative distance, IGRP's default administrative distance is 100. Administrative distance is considered the trustworthiness of the route. If you have two routing protocols with the same route the router will pick the route with the lower number. The 1 is the hops required to get to the destination network. The next piece of information is the via 172.16.10.1 that is the next hop address it must go to. The last item is that this information was learned via Serial0.
Another great command is show ip protocols. This displays information about the ip routing protocols you have enabled. Lets type the command : show ip protocols and see what we get.
Router4#show ip protocols
Looking at the output in detail we see we are sending updates every 90 seconds. We know IGRP is a distance vector routing protocol so it exchanges its entire routing table every 90 seconds. We also see our network statements are working by noticing the networks are both under the Routing for Networks area. The last area to notice is the Distance which we said was administrative distance. This tells us the default is 100 and that is what we are using.
Conclusion:
In this lab we have configured our routers for IGRP so that we can exchange information with more than the directly connected neighbor. We have learned that IGRP's metric is hop count and the routers send updates every 30 seconds be default. Now in the next lab we will go into IGRP (Interior Gateway Routing Protocol).
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved.
ROUTING INFORMATION PROTOCOL
IP Addresses: Please set these IP addresses on the interfaces of your routers.
Router1 Router2 Router4
1) Set our hostname and get our interfaces up.
2) Configure Rip routing protocol
3) Select the directly connected networks
4) View our routing table
5) View the Rip protocol information
6) Observe Rip debugging information
--------------------------------------------------------------------------------
Routing Information Protocol (RIP) is a standards-based, distance-vector, interior gateway protocol (IGP) used by routers to exchange routing information. RIP uses hop count to determine the best path between two locations. Hop count is the number of routers the packet must go through till it reaches the destination network. The maximum allowable number of hops a packet can traverse in an IP network implementing RIP is 15 hops. In a RIP network, each router broadcasts its entire RIP table to its neighboring routers every 30 seconds. When a router receives a neighbor's RIP table, it uses the information provided to update its own routing table and then sends the updated table to its neighbors. This procedure is repeated by each router and results in a state referred to as network convergence, in which all routers have an identical view of the internetwork topology.
Lets connect to Router1 and get it configured. We will be using the table above for our IP addresses.
Router>en
RIP version 1 is classful, meaning it does not include the subnet mask in its routing table updates. RIP version 2 is classless and includes the subnet information. Now lets go ahead and start the lab.
1. We first want to configure Router1 for RIP. To enable RIP as the routing protocol we only need to type: router rip We can see this below in the router output. Notice the new mode we have entered
Router1(config)#router rip
Now that we have RIP running on our Router we need to tell the router which networks it is connected to. We do this by using the network statement. What this means is every interface of our router that is directly connected to an active network needs a network number. We will have some networks using the same ip addressing schemes with different subnets, and some are using entirely different addressing schemes. Look at the diagram below. In this diagram we have three different kinds of addressing schemes. Lets look at these in more detail. On Router 1 we have an IP address of 10.1.1.1 with a /24 subnet mask. Since RIP is classful you are only required to enter the class part of the address for the network statement. For example on Router1 we have already issued the command router rip, we then need to specify the directly connected networks to Router1 so the router can advertise these routes in its routing table. To do this we would only need to type: network 10.0.0.0 now we have not told the router about the network on his serial interface, to do this we would type: network 172.16.0.0 Lets look at Router 2 what network statements do you would need to use on this router
The answers are network 10.0.0.0. The network statement for the serial link is the same for Router1 and Router2. For the network statement for the ethernet link you had to remember that a 192 address was a class C address, for this network statement you used the classful portion of the address 192.168.1.0.
Now that we understand the network command lets enter it on our Router1.
Router1(config-router)#network 172.16.0.0
If you notice we only entered 10.0.0.0 for our network statement, this is because 10.0.0.0 is a Class B address and rip only uses the classful portion of the address. Now we have configured Router1 for RIP lets connect to Router2 and get it setup.
We need to connect to Router2 and follow the same instructions. Lets select Router2 from the Window pull down menu. When we connect we are going to set a hostname to Router2, then set the ip addresses to the table above and configure RIP.
Router>en
Now add the RIP stuff!
Router2(config)#router rip
We need to connect to Router4 and follow the same instructions. Lets select Router4 from the Window pull down menu. When we connect we are going to set a hostname to Router4, then set the ip addresses to the table above and configure RIP.
Router>en
Now add the RIP stuff!
Router4(config)#router rip
Now that we have RIP running on our entire network lets verify that it is receiving routes. To do this we will be using some show commands. The most common one is show ip route. This displays all entries in the routing table. If we do this on our Router 4 we will see the route to our directly connected Router1, we will also see routes to the other routers we have setup on the network. Lets take a look at our routing table, to do this type: show ip route from the privilege mode.
Lets look at the first entry R 10.1.1.0/24 [120/1] via 172.16.10.2, 00:00:21, Serial0. It starts off with R this says it is a Rip route it then says the destination network with sunbet mask in this case it is 10.1.1.0 with a /24 (255.255.255.0) subnet mask. Next it gives 120/1 the 120 is the administrative distance, Rip's default administrative distance is 120. Administrative distance is considered the trustworthiness of the route. If you have two routing protocols with the same route the router will pick the route with the lower number. The 1 is the hops required to get to the destination network. The next piece of information is the via 172.16.10.1 that is the next hop address it must go to. The last item is that this information was learned via Serial0.
Another great command is show ip protocols. This displays information about the ip routing protocols you have enabled. Lets type the command : show ip protocols and see what we get.
Router4#show ip protocols
Router4#
Looking at the output in detail we see we are sending updates every 30 seconds. We know Rip is a distance vector routing protocol so it exchanges its entire routing table every 30 seconds. We also see our network statements are working by noticing the networks are both under the Routing for Networks area. The last area to notice is the Distance which we said was administrative distance. This tells us the default is 120 and that is what we are using.
Conclusion:
In this lab we have configured our routers for RIP so that we can exchange information with more than the directly connected neighbor. We have learned that RIP's metric is hop count and the routers send updates every 30 seconds be default. Now in the next lab we will go into IGRP (Interior Gateway Routing Protocol).
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved.
Basic IP Configuration and Verification
IP addressing is very easy to configure on a Cisco router. Although the calculation of IP addresses, subnet masks and host can be rather difficult.
The syntax to place an IP address on the interface is:
ip address ip-address mask
Given the routers below, we wish to configure IP addresses on Router1 and Router2
Remember the the /24 means 255.255.255.0. For your convenience here is a handy table:
Slash Dotted Decimal Slash Dotted Decimal Slash Dotted Decimal
/8 255.0.0.0 /16 255.255.0.0 /24 255.255.255.0
/9 255.128.0.0 /17 255.255.128.0 /25 255.255.255.128
/10 255.192.0.0 /18 255.255.192.0 /26 255.255.255.192
/11 255.224.0.0 /19 255.255.224.0 /27 255.255.255.224
/12 255.240.0.0 /20 255.255.240.0 /28 255.255.255.240
/13 255.248.0.0 /21 255.255.248.0 /29 255.255.255.248
/14 255.252.0.0 /22 255.255.252.0 /30 255.255.255.252
/15 255.254.0.0 /23 255.255.254.0 /31 255.255.255.254
Let's start configuring Router 1
Router>
Router>en
Router#conf tEnter configuration commands, one per line. End with CNTL/Z.
Router(config)#int e0
Router(config-if)#ip address 10.1.1.1 255.255.255.0
Router(config-if)#int s0
Router(config-if)#ip address 10.1.2.2 255.255.255.0
Router(config-if)#end%SYS-5-CONFIG_I: Configured from console by console
Router#
We can view the IP addresses on the interface:
Router#sh ip interface brief
Interface IP-Address OK? Method Status Protocol
BRI0 unassigned YES manual admin down down
Ethernet0 10.1.1.1 YES manual admin down down
Ethernet0 10.1.2.2 YES manual admin down down
Router#
We have assigned an IP address to each interface but the interface is still administratively down because we have not executed a 'no shutdown' command on each interface.
Now you should go to each of the interfaces and type no shutdown, this should turn the interfaces to up.
Connect to Router 2 We would also like to add ip addresses to the interfaces.
Router>
Router>en
Router#conf tEnter configuration commands, one per line. End with CNTL/Z.
Router(config)#int e0
Router(config-if)#ip address 10.1.1.2 255.255.255.0
Router(config-if)#int s0
Router(config-if)#ip address 10.1.2.2 255.255.255.0
Router(config-if)#exit%SYS-5-CONFIG_I: Configured from console by console
Router(config)#exit
Router#exit
PING
PING, the Packet Inter Net Groper, allows a user to test basic connectivity. The syntax is:
ping ip-address
The router will send out five echo requests to the destination IP address, if it receives a reply, it will not it with an '!', if not reply is received it will note it with a '.'.
A successful ping:
Router#ping 10.1.1.1
Type escape sequence to abort.Sending 5, 100-byte ICMP Echos to 10.1.1.1, timeout is 2 seconds:!!!!!
Success rate is 100 percent (5/5), round-trip min/avg/max = 32/37/44 ms
Router#
A failed ping:
Router#ping 2.2.2.2
Type escape sequence to abort.Sending 5, 100-byte ICMP Echos to 10.1.1.2, timeout is 2 seconds:.....
Success rate is 0 percent (0/5)
Router#
Ping is one of the most commonly used test tools in the word. PING uses the Internet Control Message Protocol (ICMP) to communicate with other routers.
You can also view your ip addresses using the command show running-config or show ip interface.
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved
Configuring and Examining Interfaces
Examining the Interfaces
Routers can have many types of interfaces, such as token ring, FDDI, ethernet, serial, ISDN etc. We often want to view the status and settings. There are a few important commands we must know.
show interfaces is on of the more important commands.
Router#show interfaces
Ethernet0 is administratively down, line protocol is down
Hardware is Lance, address is 0060.5cc4.f445 (bia 0060.5cc4.f445)
MTU 1500 bytes, BW 10000 Kbit, DLY 1000 usec, rely 255/255, load 1/255Encapsulation ARPA, loopback not set, keepalive set (10 sec)
[ OUTPUT OMMITTED]
This command will produce output about each interface. In this case we see that Ethernet 0 is administratively down. That means that it is turned off with the shutdown command. The different status that can occur:
Ethernet 0 is Line protocol is Meaning administratively down down The interface is turned off with the shutdown command up down Cable is connected but keep alives are not being received. down down Cabling problem or no clock rate set on DCE. Or other router interface is shutdown. up up connected and receiving keep alives. This is what we want!!!
You can view particular intefaces with the command: show interface serial 0. Or any other interface. A handy command is show ip interface brief.
Router#show ip int brief
Interface IP-Address OK? Method Status Protocol
Ethernet0 unassigned YES not set administratively down down
PCbus0 unassigned YES not set administratively down down
Serial0 unassigned YES not set up down
Router#
This allows you to rapidly see the status of all the interfaces.
Examining the Controllers
Controllers are the part of the interface that makes the physical connection. The most important to us is to find our what kind of cable is attached to a serial interface.
A DTE (data terminating equipment) cable is the normal cable you should use. Being DTE means you expect the other end to providing clocking.
A DCE data circuit-terminating equipment) means that this deving must provide the clocking on the wire.
The show controllers command will allow you to see if you are DCE or DTE.
Router#show controllers serial 0
HD unit 0, idb = 0xA2B58, driver structure at 0xA7020buffer size 1524 HD unit 0, V.35 DCE cablecpb = 0x42, eda = 0x2140, cda = 0x2000
Configuring the Interfaces
If an interface is administratively down. You must enter configuration mode, the enter interface configuration mode, and then issue the command no shutdown.
Router#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#interface ethernet 0
Router(config-if)#no shutdown
Router(config-if)#%LINEPROTO-5-UPDOWN: Line protocol on Interface Ethernet0, changed state to up%LINK-3-UPDOWN: Interface Ethernet0, changed state to up
Router(config-if)#endRouter#
If your interface is the DCE, you must provide clocking using the clock rate command.
Router#config t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#interface serial 0
Router(config-if)#clock rate 56000Router(config-if)#end
Router#
It is often useful to put a description of what the interface is used for using the description command.
Router#conf t
Enter configuration commands, one per line. End with CNTL/Z.
Router(config)#int e0
Router(config-if)#description My Connection to the Engineering Hub
Router(config-if)#end
Router#
You can view your changes using show running-config or show interfaces or show controllers
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved.
Saving your configurations using the Copy command
Running Configuration
The currently active configuration script running on the router is referred to as the 'running-config' on the routers command-line interface. Note the privilege mode required. The running configuration script is not automatically saved on a Cisco router, and will be lost in the event of power failure. The running configuration must be manually saved with the 'copy' command (discussed in a later lab).
Router>
Router>enable
Router#show running-configBuilding configuration...
Current configuration:
!version 12.0!hostname Router
!interface Serial0
no ip address
shutdown
!interface BRI0
no ip address
shutdown
!interface Ethernet0
no ip address
shutdown
!line con 0
line aux 0
line vty 0 4
!end
Router#
If you decide you would like to start configuring a router from scratch you will need to reload the router making sure you have deleted your startup-config file that is stored in NVRAM. To do this you will need to first erase the configuration file you have in NVRAM using the command erase startup-config. Next you will need to reload the router and do not save the configurations when asked.
left#erase startup-
left#erase startup-config
Erasing the nvram filesystem will remove all files! Continue? [confirm][OK]Erase of nvram: complete
left#reload
System configuration has been modified. Save? [yes/no]: n
Proceed with reload? [confirm]
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved.
The Cisco Discovery Protocol (CDP) Discovery Protocol
CDP allows devices to share basic configuration information without even configuring any protocol specific information. CDP is enabled by default on all interfaces.
CDP is a Datalink Protocol occuring at Layer 2 of the OSI model. This is important to understand because CDP is not routable. It can only traverse to directly connected devices.
CDP allows you to view information such Operating System Version, Protocol Information, and much more. This can be very handy for troubleshooting a variety of problems.
CDP ConfigurationBy default it is enabled on the router and all interfaces. The commands are simple:
Global Configuration Commands:
no cdp run turn off CDP for the entire router cdp run (default) turn it on for the entire router cdp timer 120 would change CDP to advertise every 120 seconds
Interface Configuration Commands:
cdp enable (default) turn it on for the interface no cdp enable turn it off for interface
Show Commands:
show cdp interface view interface settings,
show cdp neighbor view directly connected neighbors
show cdp neighbor detail view detailed information about neighbors show cdp general information Copyright (c) 2001 Boson Software, Inc. All Rights Reserved.
Show Lab Overview 2
This lab will introduce the Cisco Internetwork Operating System (IOS) command line interface (CLI). You will need to logon to a router and become familiar with the different levels of access on the router. You will also become familiar with the commands available to you in each mode (user or privileged) and the router help facility, history, and editing features.
Show Version
The 'show version' command gives you a lot more information than at first you may think. Use 'show version' to obtain critical information, such as: router platform type, operating system revision, operating system last boot time and file location, amount of memory, number of interfaces, and configuration register.
Router>show version
Krang Operating System SoftwareRouter
uptime is 2 minutesSystem returned to
ROM by power-onSystem image file is "flash:c2500.bin"
[[[OUTPUT DELETED]]]
1 Ethernet/IEEE 802.3 interface(s)
1 Serial(sync/async) network interface(s)
1 ISDN Basic Rate interface(s)
32K bytes of non-volatile configuration memory.
4096K bytes of processor board System flash (Read/Write)
Configuration register is 0x2102
Routing Protocols
To view the status of any routing protocols currently configured on the router, use the 'show protocols' command.
Router>show protocols
Global values:
Internet Protocol routing is enabled
BRI0 is administratively down, line protocol is Down
Ethernet0 is administratively down, line protocol is Down
Serial0 is administratively down, line protocol is Down
Flash Memory
Flash memory is a special kind of memory on the router that contains the operating system image file(s). Unlike regular router memory, Flash memory continues to maintain the file image even after power is lost.
Router>show flash
System flash directory:
File Length Name/status1 3015588 c2500.bin
[3015652 bytes used, 1178652 available, 4194304 total]
4096K bytes of processor board System flash (Read/Write)
Running Configuration
The currently active configuration script running on the router is referred to as the 'running-config' on the routers command-line interface. Note the privilege mode required. The running configuration script is not automatically saved on a Cisco router, and will be lost in the event of power failure. The running configuration must be manually saved with the 'copy' command (discussed in a later lab).
Router>
Router>enable
Router#show running-configBuilding configuration...
Current configuration:
!version 12.0
!hostname Router
!interface Serial0
no ip address
shutdown
!interface BRI0
no ip address
shutdown
!interface Ethernet0
no ip address
shutdown
!line con 0
line aux 0
line vty 0 4
!end
Router#
Command History
The routers Command Line Interface (CLI) maintains by default the last 10 commands you have entered in memory, for later retrieval. You can change this default value. You cycle through previous router commands entered (since the last power loss), using one of two methods. To view all of the past commands still in router memory at the same time, use the 'show history' command. For single line retrieval, use either the Arrow-Up (for previous command) and Arrow-Down (for next command), or Control-P (for previous command) and Control-N (for next command).
Router>show history
show version
show protocols
show flashenable
show running-configdisable
show history
Clock
The router keeps its own clock that you can use to synchronize devices to. To view the clock use the show clock command.
Krang#show clock
*00:38:35.755 UTC Mon Mar 1 1993
Krang#
Host Table
You can create a list of host name on your router. You can view the entries (if any) by typing show hosts.
Krang#show hosts
Default domain is not setName/address lookup uses static mappings
Host Flags Age Type Address(es)Krang#
Show users
The show users command displays users who are connected to the router.
Krang#show users
Line User Host(s) Idle Location
* 0 con 0 idle 00:00:00
Krang#
Show Interfaces
The show interfaces command will display statistics for all interfaces configured on the router
Krang#show interfaces
BRI0 is administratively down, line protocol is down
Hardware is BRI
MTU 1500 bytes, BW 64 Kbit, DLY 20000 usec, rely 255/255, load 1/255
Encapsulation HDLC, loopback not setLast input never, output never, output hang never
Last clearing of "show interface" counters never
Input queue: 0/75/0 (size/max/drops); Total output drops: 0
Queueing strategy: weighted fair
Output queue: 0/1000/64/0 (size/max total/threshold/drops)
Conversations 0/0/256 (active/max active/max total)
Reserved Conversations 0/0 (allocated/max allocated)5 minute input rate 0 bits/sec, 0 packets/sec5 minute output rate 0 bits/sec, 0 packets/sec0 packets input, 0 bytes, 0 no bufferReceived 0 broadcasts, 0 runts, 0 giants, 0 throttles0 input errors, 0 CRC, 0 frame, 0 overrun, 0 ignored, 0 abort0 packets output, 0 bytes, 0 underruns0 output errors, 0 collisions, 5 interface resets0 output buffer failures, 0 output buffers swapped out0 carrier transitions--More--
Notice the --More-- This means that there is more information pertaining to the last command. To view more commands line by line, press: enter To exit the output and return to the router prompt, press: e (this can be any letter, it's just easy to remember that e is for exit) To view more output one screen at a time, press the space bar
Show Protocols
The show protocols displays global and interface specific status of layer 3 protocols.
Krang#show protocols
Global values:
Internet Protocol routing is enabled
BRI0 is administratively down, line protocol is down
Ethernet0 is administratively down, line protocol is down
Serial0 is administratively down, line protocol is down
Serial1 is administratively down, line protocol is down
Serial2 is administratively down, line protocol is down
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved.
Basic Lab Overview
This lab will introduce the Cisco Internetwork Operating System (IOS) command line interface (CLI). You will need to logon to a router and become familiar with the different levels of access on the router. You will also become familiar with the commands available to you in each mode (user or privileged) and the router help facility, history, and editing features.
User vs. Privileged Mode
User mode is indicated with the '>' next to the router name. You can look at settings but can not make changes from user mode. In Privilege mode (indicated by the '#', you can do anything. To get into privilege mode the keyword is ENABLE.
Router>
Router>enable
Password:
Router#
HELP
To view all commands available from this mode type: ? and press: enter This will give you the list of all available commands for the router in your current mode. You can also use the question mark after you have started typing a command. For example if you want to use a show command but you do not remember which one it it use show ? this will output all commands that you can use with the show command.
r1#show ?
access-expression List access expressionaccess-lists List access listsbackup Backup statuscdp CDP informationclock Display the system clockcls DLC user informationcompress Show compression statisticsconfiguration Contents of Non-Volatile memory--More--
Configuration Mode
From privilege mode you can enter configuration mode by typing CONFIG T you can exit configuration mode type type
END or
Router#config t
Router(config)#end
Copyright (c) 2001 Boson Software, Inc. All Rights Reserved
Positioning MPLS Mas mudji di mudji.net
Wednesday, August 27, 2008
Dokumen ini berisi komponen teknologi Multi-Protocol Label Switching (MPLS), fungsi-fungsinya dan ilustrasi nilai tambah bagi Service Provider.
MPLS pada mulanya ditargetkan untuk pelanggan Service Provider; tetapi saat ini perusahaan-perusahaan sudah mulai tertarik untuk penerapan teknologi ini. Dokumen ini dapat diterapkan untuk perusahaan besar yang memiliki jaringan seperti Service Provider pada area berikut ini :
- - Size/ukuran besarnya jaringan
- - Menawarkan “internal services” untuk department yang berbeda dalam perusahaan
MPLS komplimen dengan teknologi IP. MPLS di desain untuk membangkitkan kecerdasan yang berhubungan dengan IP Routing, dan Paradigma Switching yang berhubungan dengan Asynchronous Transfer Mode (ATM).
MPLS terdiri dari Control Plane dan Forwarding Plane. Control Plane membuat apa yang disebut “Forwarding Table”, sementara Forwarding Plane meneruskan paket ke interface tertentu (berdasarkan Forwarding Table).
Efisien desain dari MPLS adalah menggunakan Labels untuk membungkus/encapsulate paket IP. Sebuah Forwarding Table berisi list/mengurutkan Nilai-nalai Label (Label Values), yang masing-masing berhubungan dengan penentuan “outgoing interface” untuk setiap prefix network/jaringan.
Cisco IOS Software support 2 mekanisme signalling untuk distribusi Label: Label Distribution Protocol (LDP) dan Resource Reservation Protocol/Traffic Engineering (RSVP/TE).
MPLS meliputi komponen utama sebagai berikut :
1. MPLS Virtual Private Networks (VPNs) - memberikan “MPLS-enabled IP networks” untuk koneksi Layer 3 dan Layer 2. Berisi 2 komponen utama :
- Layer 3 VPNs - menggunakan Border Gateway Protocol.
- Layer 2 VPNs - Any Transport over MPLS (AToM)
2. MPLS Traffic Engineering (TE) - menyediakan peningkatan utilisasi dari bandwidth jaringan yang ada dan untuk “protection services”.
3. MPLS Quality of Service (QoS) - menggunakan mekanisme IP QoS existing, dan menyediakan perlakuan istimewa untuk type trafik tertentu, berdasarkan atribut QoS (seperti MPLS EXP)
MPLS VPNs
Layer 3 VPNs
Layer 3 VPNs atau BGP VPNs, teknologi MPLS yang paling banyak digunakan. Layer 3 VPNs menggunakan “Virtual Routing instances” untuk membuat sebuah pemisahan table routing untuk tiap-tiap pelanggan/subscriber, dan menggunakan BGP untuk membentuk koneksi (peering relations) dan signal VPN-berLabel dengan masing-masing router Provider Edge (PE) yang sesuai. Hasilnya sangat scalable untuk diimplementasikan, karena router core (P) tidak memiliki informasi tentang VPNs.
BGP VPNs sangat berguna ketika pelanggan menginginkan koneksi Layer 3 (IP), dan lebih menyukai untuk membuang overhead routing ke Service Provider. Hal ini menjamin bahwa keanekaragaman interface Layer 2 dapat digunakan pada tiap sisi/side VPN. Contoh, Site A menggunakan interface Ethernet, sementara Site B menggunakan interface ATM; Site A dan Site B adalah bagian dari single VPN.
Relatif sederhana untuk penerapan “multiple topologies” dengan “router filtering”, Hub & Spoke atau Full Mesh:
Hub and Spoke - “central site” dikonfigurasi untuk “learn/mempelajari” semua “routes” dari seluruh remote sites, sementara remote sites dibatasi untuk “learn/mempelajari” routes, hanya khusus dari central site.
Topology Full Mesh akan menciptakan semua sites mempunyai kemampuan “learn/mempelajari” atau mengimport routes dari tiap site lainnya.
Layer 3 VPNs telah dikembangkan dalam jaringan yang mempunyai router PE sebanyak 700. Saat ini terdapat Service Provider yang memiliki sampai 500 VPNs, dengan masing-masing VPN berisi site sebanyak 1000. Banyak ragam routing protocol yang digunakan pada link akses pelanggan (yaitu link CE ke PE); Static Routes, BGP, RIP dan Open Shortest Path First (OSPF). VPNs paling banyak menggunakan Static Routes, diikuti dengan Routing BGP.
Layer 3 VPNs menawarkan kemampuan lebih, seperti Inter-AS dan Carrier Supporting Carrier (CSC). Hierarchical VPNs, memungkinkan Service Provider menyediakan koneksi melewati “multiple administrative networks”. Saat ini, penerapan awal dari fungsi seperti ini sudah tersebar luas.
Layer 2 VPNs
Layer 2 VPNs mengacu pada kemampuan dan kebutuhan dari pelanggan Service Provider untuk menyediakan Layer 2 Circuits melalui “MPLS-enabled IP backbone”. Penting untuk memahami 3 komponen utama dari Layer 2 VPNs:
Layer 2 Transport over over MPLS - Layer 2 circuit - membawa data secara transparent - melalui MPLS enabled IP backbone (juga dikenal sebagai AToM).
Virtual Private Wire Services - Kemampuan untuk menambahkan signalling ke AToM, dan untuk fitur-fitur seperti auto-discovery perangkat CE.
Virtual Private LAN Services - Kemampuan menambahkan Virtual Switch Instances (VSIs) pada router PE untuk membentuk “LAN based services” melalui MPLS-enabled IP backbone.
Circuits Layer 2 yang dominan adalah Ethernet, ATM, Frame Relay, PPP, dan HDLC. AToM dan Layer 3 VPNs didasarkan pada konsep yang sama, tetapi AToM menggunakan sebuah “directed LDP session” untuk mendistribusikan Labels VC (analogy dengan BGP VPN Label). Oleh karena itu, router core tidak perlu mengetahui per-subscriber basis, hasinya sebuah architecture yang sangat “scalable”.
Sebelum ada AToM, Service Provider harus membangun jaringan yang berbeda untuk menyediakan koneksi Layer 2. Contoh, Service Provider harus membangun sebuah ATM dan sebuah Frame Relay Network, hasilnya peningkatan biaya operasional dan “capital expenses”. Saat ini, Layer 2 VPNs MPLS memungkinkan Service Provider untuk menggabungkan jenis jaringan yang berbeda ini, sehingga menghemat biaya operasional dan “capital expenses” secara significant.
Layer 2 VPNs dan Layer 3 VPNs dapat dikonfigurasi dalam single/satu box dan dapat difungsikan untuk meningkatkan keuntungan dari pelanggan.
Layer 2 dan Layer 3 VPNs saling melengkapi satu sama lain. Dengan berjalannya waktu, demand untuk Layer 2 VPNs bisa jadi lebih tinggi dibandingkan dengan Layer 3 VPNs.
MPLS Traffic Engineering
MPLS TE sejak awal diharapkan Service Provider sebagai teknologi yang dapat memanfaatkan bandwitdh jaringan yang tersedia secara lebih baik dengan menggunakan jalur alternatif/alternate paths (selain dari “the shortest path).
MPLS TE telah dikembangkan dengan beberapa keuntungan, termasuk Connectivity Protection menggunakan Fast ReRoute dan “Tight QoS”. “Tight QoS” dihasilkan dari penggunaan MPLS TE dan mekanisme QoS secara bersamaan.
MPLS TE menggunakan IGP, IS-IS dan OSPF untuk menyebar informasi bandwidth melalui jaringan. MPLS TE juga menggunakan RSVP Extention untuk mendistribusikan label dan “constraint-based routing” untuk menghitung jalur/paths dalam jaringan. Extention ini telah didefinisikan di rfc 3209
Service Provider yang membangun MPLS cenderung untuk menerapkan “full mesh” TE Tunnels, menciptakan logical mesh, walaupun topology physical tidak full mesh. Pada situasi seperti ini, Service Provider telah memperolah tambahan 40% - 50% ketersediaan bandiwidth di jaringan. Keuntungan ini adalah penggunaan jaringan secara optimal, yang berperan penting pada penurunan “capital expenses”.
MPLS TE menyediakan Connectivity Protection menggunakan Fast ReRoute (FRR). FRR memproteksi primary tunnels menggunakan pre-provisioned backup tunnels. Jika tunnel DOWN (failure condition), dibutuhkan waktu sekitar 50 ms untuk primary tunnel “switch over” ke backup tunnel. FRR bergantung pada proteksi Layer 3, tidak seperti proteksi SONET atau SDH yang terjadi pada level interface. Oleh karena itu, Waktu restorasi bergantung pada jumlah tunel dan jumlah prefix yang di”switch-over”. Ini adalah hal penting (key issue) yang harus dipertimbangkan ketika membuat desain FRR yang optimal.
Test internal implementasi FRR Cisco telah menghasilkan performansi lebih baik dari 50 ms; walau bagaimanapun, waktu restorasi mungkin lebih tinggi, bergantung pada konfigurasi. FRR dapat digunakan untuk proteksi Links, Nodes dan seluruh LSP Path. Sebagian besar Service Provider lebih memperhatikan local failures, dan banyak ditemukan bahwa link failures lebih sering terjadi daripada node failures.
DiffServ Aware Traffic Engineering mampu menjalankan TE untuk class trafik yang berbeda. Service Provider boleh memutuskan untuk mengoperasikan TE Tunnels yang memanfaatkan “sub-pool” untuk trafik Voice. Selanjutnya, Service Provider dapat menyakinkan bahwa tunnel ini menggunakan explicit path, dimana shortest path menghasilkan delay terpendek. Selain itu, terdapat TE Tunnels yang menggunakan “global pool” untuk trafik non-voice yang bukan “delay sensitive”.
Hal ini penting untuk dicatat bahwa MPLS TE adalah fungsi dari Control Plane. Ketika solusi Virtual Leased Line (VLL) didefinisikan, mekanisme QoS yang sesuai harus dikonfigurasi (seperti Queuing atau Policing) untuk memenuhi garansi bandiwidth. Service Provider sudah mulai menawarkan jasa VLL sebagai trunk voice untuk menghubungkan Central Office termasuk PBX.
MPLS Quality of Service
MPLS QoS mempengaruhi mekanisme existing dari IP QoS DiffServ, memungkinkan mereka bekerja pada jalur/path MPLS. Extension tertentu, termasuk kemampuan untuk melakukan “set” dan “match” pada bit-bit MPLS EXP telah ditambahkan; meskipun “fundamental behavior” dari mekanisme QoS tetap tidak berubah.
MPLS secara fundamental adalah teknik “tunneling”, jadi mekanisme QoS memungkinkan untuk penerapan yang flexible dengan “tunneling” QoS pelanggan melalui policies QoS dari Service Provider.
Oleh karena itu, Service Provider seharusnya menggunakan nilai EXP 6 untuk voice, dan nilai EXP 4 dan 3 untuk trafik non-voice. Menyediakan transparent services secara simultan untuk Enterprise dengan Maps QoS sebagai berikut :
- Menggunakan Prec 3 untuk voice dan Prec 2 untuk trafik non-voice
- Menggunakan Prec 5 untuk voice dan Prec 4 untuk trafic non-voice
Penawaran service QoS pada MPLS VPN telah menjadi nilai tambah bagi Service Provider, tetapi penerapan QoS bervariasi antar customer. Beberapa customer membuat hanya 2 class of services - (voice dan non-voice), sementara lainnya membuat sebanyak 5 class :
• Best Effort Data
• Interactive Data (i.e.,Telnet)
• Mission Critical Data (ERP applications; i.e., SAP, PeopleSoft)
• Video
• Voice
Kesimpulan
MPLS sedang berkembang sebagai teknologi yang dapat diterima secara luas, dibuktikan dengan lebih dari 100 customers menerapkan Cisco MPLS. Hal ini penting untuk dicatat bahwa MPLS tidak menggantikan IP. IP Control Plane adalah komponen fundamental MPLS. Kemampuan menambahkan “ATM-like Forwarding Plane” membuatnya menarik bagi Service Provider dan Enterprises.
Service Provider bisa mendapatkan keuntungan sebesar 25% dengan menerapkan MPLS VPNs, MPLS QoS dan MPLS TE, daripada sekedar menyediakan koneksi VPNs biasa.
Kesimpulan akhir adalah, keuntungan utama bagi Service Provider dan Enterprises menerapakan MPLS-enabled IP Network adalah kemampuan menyediakan koneksi Layer 3 dan Layer 2 dan “shared services” (seperti DHCP, NAT, dll) melalui “single network”, dengan tingkat optimasi dan utilisasi yang tinggi dari bandwidth yang tersedia menggunakan TE dan QoS.
2 Speedy on 1 router
Sunday, July 13, 20081. Ip address setting
/ip address
add address=192.168.0.254/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local comment="Link to Local Lan" disabled=no
add address=192.168.1.2/24 network=192.168.1.0 broadcast=192.168.255 interface=speedy1 comment="Link to Modem 1" disabled=no
add address=192.168.2.2/24 network=192.168.2.0 broadcast=192.168.2.255 interface=speedy2 comment="Link to Modem 2" disabled=no
2. Manggle setting for NTH concept and packet mark
/ip firewall mangle
add chain=prerouting in-interface=Local connection-state=new nth=1,2,0 action=mark-connection new-connection-mark=link1 passthrough=yes comment="Mark Nth for link 1" disabled=no
add chain=prerouting in-interface=Local connection-mark=link1 action=mark-routing new-routing-mark=link1 passthrough=no comment="" disabled=no
add chain=prerouting in-interface=Local connection-state=new nth=1,2,1 action=mark-connection new-connection-mark=link2 passthrough=yes comment="Mark Nth for link 1" disabled=no
add chain=prerouting in-interface=Local connection-mark=link2 action=mark-routing new-routing-mark=link2 passthrough=no comment="" disabled=no
3. Nat tables for Link1 and link 2
/ip firewall nat
add chain=srcnat connection-mark=link1 action=src-nat to-addresses=192.168.1.2 to-ports=0-65535 comment="Masquee Nat Link 1" disabled=no
add chain=srcnat connection-mark=link2 action=src-nat to-addresses=192.168.2.2 to-ports=0-65535 comment="Masquee Nat Link 2" disabled=no
4. Ip routing for link 1 and 2
/ ip route
add dst-address=0.0.0.0/0 gateway=192.168.1.1 scope=255 target-scope=10 routing-mark=link1 comment="Link To modem1" disabled=no
add dst-address=0.0.0.0/0 gateway=192.168.2.2 scope=255 target-scope=10 routing-mark=link2 comment="Link To modem1" disabled=no
add dst-address=0.0.0.0/0 gateway=192.168.2.2 scope=255 target-scope=10 comment="Default routing" disabled=no <<-- this default routing simple configuration load balancing.
Spanning Tree Protocol (STP)
Saturday, July 12, 2008Spanning Tree Protocol (STP)
Back before it was purchased and renamed Compaq, a company called Digital Equipment Corporation (DEC) created the original version of Spanning Tree Protocol (STP) . The IEEE later created its own version of STP called 802.1D. All Cisco switches run the IEEE 802.1D version of STP, which isn’t compatible with the DEC version.
STP’s main task is to stop network loops from occurring on your layer 2 network (bridges or switches). It vigilantly monitors the network to find all links, making sure that no loops occur by shutting down any redundant links. STP uses the spanning-tree algorithm (STA) to first create a topology database, then search out and destroy redundant links. With STP running, frames will only be forwarded on the premium, STP-picked links. In the following sections, I am going to hit the nitty-gritty of the Spanning Tree Protocol.
Spanning Tree Terms
Before I get into describing the details of how STP works in the network, you need to understand some basic ideas and terms and how they relate within the layer 2 switched network:
STP
Spanning Tree Protocol (STP) is a bridge protocol that uses the STA to find redundant links dynamically and create a spanning-tree topology database. Bridges exchange BPDU messages with other bridges to detect loops, and then remove them by shutting down selected bridge interfaces.
Root bridge
The root bridge is the bridge with the best bridge ID. With STP, the key is for all the switches in the network to elect a root bridge that becomes the focal point in the network. All other decisions in the network—such as which port is to be blocked and which port is to be put in forwarding mode—are made from the perspective of this root bridge.
BPDU
All the switches exchange information to use in the selection of the root switch, as well as in subsequent configuration of the network. Each switch compares the parameters in the Bridge Protocol Data Unit (BPDU) that they send to one neighbor with the one that they receive from another neighbor.
Bridge ID The bridge ID is how STP keeps track of all the switches in the network. It is determined by a combination of the bridge priority (32,768 by default on all Cisco switches) and the base MAC address. The bridge with the lowest bridge ID becomes the root bridge in the network.
Nonroot bridge These are all bridges that are not the root bridge. Nonroot bridges exchange BPDUs with all bridges and update the STP topology database on all switches, preventing loops and providing a measure of defense against link failures.
Root port The root port is always the link directly connected to the root bridge, or the shortest path to the root bridge. If more than one link connects to the root bridge, then a port cost is determined by checking the bandwidth of each link. The lowest cost port becomes the root port. If multiple links have the same cost, the bridge with the lower advertising bridge ID is use. Since multiple links can be from the same device, the lowest port number will be used.
Designated port A port that has been determined as having the best (lower) cost—a designated port will be marked as a forwarding port.
Port cost Port cost determines when multiple links are used between two switches and none are root ports. The cost of a link is determined by the bandwidth of a link.
Nondesignated port Port with a higher cost than the designated port that will be put in blocking mode—a nondesignated port is not a forwarding port.
Forwarding port A forwarding port forwards frames.
Blocked port A blocked port is the port that will not forward frames, in order to prevent loops. However, a blocked port will always listen to frames.
Spanning Tree Operations
As I’ve said before, STP’s job is to find all links in the network and shut down any redundant ones, thereby preventing network loops from occurring. STP does this by first electing a root bridge that will preside over network topology decisions. Once all switches agree on who the root bridge is, every bridge must find the root port. If there are multiple links between switches, there must be one and only one designated port.
Things tend to go a lot more smoothly when you don’t have more than one person making a navigational decision, and so, there can only be one root bridge in any given network. I’ll discuss the root bridge election process more completely in the next section.
Selecting the Root Bridge
The bridge ID is used to elect the root bridge in the STP domain as well as to determine the root port. This ID is 8 bytes long, and includes both the priority and the MAC address of the device. The default priority on all devices running the IEEE STP version is 32,768.
To determine the root bridge, the priority of each bridge is combined with its MAC address. If two switches or bridges happen to have the same priority value, then the MAC address becomes the tie breaker for figuring out which one has the lowest (best) ID. It’s like this: If two switches— I’ll name them A and B—both use the default priority of 32,768, then the MAC address will be used instead. If Switch A’s MAC address is 0000.0c00.1111 and Switch B’s MAC address is 0000.0c00.2222, then Switch A would become the root bridge. Just remember that the lower value is the better one when it comes to electing a root bridge.
BPDUs are sent every 2 seconds, by default, out all active ports on a bridge/switch, and the bridge with the lowest (best) bridge ID is elected the root bridge. You can change the bridge’s ID by lowering its priority so that it will become a root bridge automatically. Being able to do that is important in a large switched network—it ensures that the best paths are chosen.
| Note : Changing STP parameters is beyond the scope of this book, but it’s covered in CCNP: Building Cisco Multilayer Switched Networks |
Selecting the Designated Port
If more than one link is connected to the root bridge, then port cost becomes the factor used to determine which port will be the root port. So, to determine the port that will be used to communicate with the root bridge, you must first figure out the path’s cost. The STP cost is an accumulated total path cost based on the available bandwidth of each of the links. Table 3.1 shows the typical costs associated with various Ethernet networks.
TABLE 3.1 Typical Costs of Different Ethernet Networks
The IEEE 802.1D specification has recently been revised to handle the new higher-speed links. The IEEE 802.1D specification assigns a default port cost value to each port based on bandwidth.
Spanning-Tree Port States
The ports on a bridge or switch running STP can transition through five different states:
Blocking A blocked port won’t forward frames; it just listens to BPDUs. The purpose of the blocking state is to prevent the use of looped paths. All ports are in blocking state by default when the switch is powered up.
Listening The port listens to BPDUs to make sure no loops occur on the network before passing data frames. A port in listening state prepares to forward data frames without populating the MAC address table.
Learning The switch port listens to BPDUs and learns all the paths in the switched network. A port in learning state populates the MAC address table but doesn’t forward data frames.
Forwarding The port sends and receives all data frames on the bridged port. If the port is still a designated or root port at the end of the Learning state, it enters this state.
Disabled A port in the disabled state (administratively) does not participate in the frame forwarding or STP. A port in the disabled state is virtually nonoperational.
Switch ports are most often in either the blocking or forwarding state. A forwarding port is one that has been determined to have the lowest (best) cost to the root bridge. But when and if the network experiences a topology change (because of a failed link or because someone adds in a new switch), you’ll find the ports on a switch in listening and learning state.
As I mentioned, blocking ports is a strategy for preventing network loops. Once a switch determines the best path to the root bridge, then all other ports will be in blocking mode. Blocked ports can still receive BPDUs—they just don’t send out any frames.
If a switch determines that a blocked port should now be the designated or root port because of a topology change, it will go into listening mode and check all BPDUs it receives to make sure that it won’t create a loop once the port goes to forwarding mode.
Convergence
Convergence occurs when all ports on bridges and switches have transitioned to either the forwarding or blocking modes. No data is forwarded until convergence is complete. Before data can be forwarded again, all devices must be updated. Convergence is important to make sure all devices have the same database, but it does cost you some time. It usually takes 50 seconds to go from blocking to forwarding mode, and I don’t recommend changing the default STP timers. (But you can adjust those timers if necessary.) Forward delay means the time it takes to transition a port from listening to learning mode or vice versa.
Spanning Tree Example
It’s time to begin using and not just reading about this stuff. It’s important to see how a spanning tree works in an internetwork, because it will really help you understand it better. So in this section, I’ll give you a chance to observe what you’ve learned as it takes place in a live network.
In Figure 3.1, you can assume that all five switches have the same priority of 32,768. But now study the MAC address of each switch. By looking at the priority and MAC addresses of each device, you should be able to determine the root bridge:
Once you’ve established which switch has got to be the root bridge, look at the figure again and try to figure out which is the root port on each of the switches. (Hint: Root ports are always forwarding ports, which means they will always be in forwarding mode.) Okay, next try to establish which of the ports will be in blocking mode.
FIGURE 3.1 Spanning tree example
Figure .3.2 has the answers for each of the port states for each switch. Since Switch A has the lowest MAC address, and all five switches use the default priority, Switch A gets to be the root bridge. And remember this: A root bridge always has every port in forwarding mode (designated ports).
To determine the root ports on Switch B and Switch C, just follow the connection to the root bridge. Each direct connection to the root bridge will be a root port, so it will become forwarding. On Switches D and E, the ports connected to Switches B and C are Switches D and E’s closest ports to the root bridge (lowest cost), so those ports are root ports and in forwarding mode.
Take another look at the Figure 3.2. Can you tell which of the ports between Switch D and E must be shut down so a network loop doesn’t occur? Let’s work it out: Since the connection from Switches D and E to Switches B and C are root ports, those can’t be shut down. Next, the bridge ID is used to determine designated and nondesignated ports; so, because Switch D has the lowest (best) bridge ID, Switch E’s port to Switch D will become nondesignated (blocking), and Switch D’s connection to Switch E will be designated (forwarding).
FIGURE 3.2 Spanning tree example answers
When should I worry about spanning tree?
Bob, a Senior Network Administrator at Acme Corporation in San Francisco, is concerned about all the new switches his bosses just asked him to install, which will bring the total number of switches in his network to 20. He is concerned about STP and isn’t sure if he should even think about it since it seems to work OK with the few switches he has installed. Bob calls you for advice. What should you tell Bob when he calls?
If you have fewer than six switches in your internetwork and no more than about 100 users in your network, you would usually just let STP do its job and not worry about it. Understand that each network may vary, but with Bob ending up with about 20 switches, he has to think about STP!
But if you have dozens of switches and hundreds of users in your network, then it’s time to pay attention to how STP is running. That’s because if you don’t set the root switch in this larger switched network, your STP may never converge between switches—a nasty situation that could bring your network down.
Setting the timers and root switch are covered in the CCNP: Building Cisco Multilayer Switched Networks
Spanning Tree Protocol (STP)
Spanning Tree Protocol (STP)
Back before it was purchased and renamed Compaq, a company called Digital Equipment Corporation (DEC) created the original version of Spanning Tree Protocol (STP) . The IEEE later created its own version of STP called 802.1D. All Cisco switches run the IEEE 802.1D version of STP, which isn’t compatible with the DEC version.
STP’s main task is to stop network loops from occurring on your layer 2 network (bridges or switches). It vigilantly monitors the network to find all links, making sure that no loops occur by shutting down any redundant links. STP uses the spanning-tree algorithm (STA) to first create a topology database, then search out and destroy redundant links. With STP running, frames will only be forwarded on the premium, STP-picked links. In the following sections, I am going to hit the nitty-gritty of the Spanning Tree Protocol.
Spanning Tree Terms
Before I get into describing the details of how STP works in the network, you need to understand some basic ideas and terms and how they relate within the layer 2 switched network:
STP
Spanning Tree Protocol (STP) is a bridge protocol that uses the STA to find redundant links dynamically and create a spanning-tree topology database. Bridges exchange BPDU messages with other bridges to detect loops, and then remove them by shutting down selected bridge interfaces.
Root bridge
The root bridge is the bridge with the best bridge ID. With STP, the key is for all the switches in the network to elect a root bridge that becomes the focal point in the network. All other decisions in the network—such as which port is to be blocked and which port is to be put in forwarding mode—are made from the perspective of this root bridge.
BPDU
All the switches exchange information to use in the selection of the root switch, as well as in subsequent configuration of the network. Each switch compares the parameters in the Bridge Protocol Data Unit (BPDU) that they send to one neighbor with the one that they receive from another neighbor.
Bridge ID The bridge ID is how STP keeps track of all the switches in the network. It is determined by a combination of the bridge priority (32,768 by default on all Cisco switches) and the base MAC address. The bridge with the lowest bridge ID becomes the root bridge in the network.
Nonroot bridge These are all bridges that are not the root bridge. Nonroot bridges exchange BPDUs with all bridges and update the STP topology database on all switches, preventing loops and providing a measure of defense against link failures.
Root port The root port is always the link directly connected to the root bridge, or the shortest path to the root bridge. If more than one link connects to the root bridge, then a port cost is determined by checking the bandwidth of each link. The lowest cost port becomes the root port. If multiple links have the same cost, the bridge with the lower advertising bridge ID is use. Since multiple links can be from the same device, the lowest port number will be used.
Designated port A port that has been determined as having the best (lower) cost—a designated port will be marked as a forwarding port.
Port cost Port cost determines when multiple links are used between two switches and none are root ports. The cost of a link is determined by the bandwidth of a link.
Nondesignated port Port with a higher cost than the designated port that will be put in blocking mode—a nondesignated port is not a forwarding port.
Forwarding port A forwarding port forwards frames.
Blocked port A blocked port is the port that will not forward frames, in order to prevent loops. However, a blocked port will always listen to frames.
Spanning Tree Operations
As I’ve said before, STP’s job is to find all links in the network and shut down any redundant ones, thereby preventing network loops from occurring. STP does this by first electing a root bridge that will preside over network topology decisions. Once all switches agree on who the root bridge is, every bridge must find the root port. If there are multiple links between switches, there must be one and only one designated port.
Things tend to go a lot more smoothly when you don’t have more than one person making a navigational decision, and so, there can only be one root bridge in any given network. I’ll discuss the root bridge election process more completely in the next section.
Selecting the Root Bridge
The bridge ID is used to elect the root bridge in the STP domain as well as to determine the root port. This ID is 8 bytes long, and includes both the priority and the MAC address of the device. The default priority on all devices running the IEEE STP version is 32,768.
To determine the root bridge, the priority of each bridge is combined with its MAC address. If two switches or bridges happen to have the same priority value, then the MAC address becomes the tie breaker for figuring out which one has the lowest (best) ID. It’s like this: If two switches— I’ll name them A and B—both use the default priority of 32,768, then the MAC address will be used instead. If Switch A’s MAC address is 0000.0c00.1111 and Switch B’s MAC address is 0000.0c00.2222, then Switch A would become the root bridge. Just remember that the lower value is the better one when it comes to electing a root bridge.
BPDUs are sent every 2 seconds, by default, out all active ports on a bridge/switch, and the bridge with the lowest (best) bridge ID is elected the root bridge. You can change the bridge’s ID by lowering its priority so that it will become a root bridge automatically. Being able to do that is important in a large switched network—it ensures that the best paths are chosen.
| Note : Changing STP parameters is beyond the scope of this book, but it’s covered in CCNP: Building Cisco Multilayer Switched Networks |
Selecting the Designated Port
If more than one link is connected to the root bridge, then port cost becomes the factor used to determine which port will be the root port. So, to determine the port that will be used to communicate with the root bridge, you must first figure out the path’s cost. The STP cost is an accumulated total path cost based on the available bandwidth of each of the links. Table 3.1 shows the typical costs associated with various Ethernet networks.
TABLE 3.1 Typical Costs of Different Ethernet Networks
The IEEE 802.1D specification has recently been revised to handle the new higher-speed links. The IEEE 802.1D specification assigns a default port cost value to each port based on bandwidth.
Spanning-Tree Port States
The ports on a bridge or switch running STP can transition through five different states:
Blocking A blocked port won’t forward frames; it just listens to BPDUs. The purpose of the blocking state is to prevent the use of looped paths. All ports are in blocking state by default when the switch is powered up.
Listening The port listens to BPDUs to make sure no loops occur on the network before passing data frames. A port in listening state prepares to forward data frames without populating the MAC address table.
Learning The switch port listens to BPDUs and learns all the paths in the switched network. A port in learning state populates the MAC address table but doesn’t forward data frames.
Forwarding The port sends and receives all data frames on the bridged port. If the port is still a designated or root port at the end of the Learning state, it enters this state.
Disabled A port in the disabled state (administratively) does not participate in the frame forwarding or STP. A port in the disabled state is virtually nonoperational.
Switch ports are most often in either the blocking or forwarding state. A forwarding port is one that has been determined to have the lowest (best) cost to the root bridge. But when and if the network experiences a topology change (because of a failed link or because someone adds in a new switch), you’ll find the ports on a switch in listening and learning state.
As I mentioned, blocking ports is a strategy for preventing network loops. Once a switch determines the best path to the root bridge, then all other ports will be in blocking mode. Blocked ports can still receive BPDUs—they just don’t send out any frames.
If a switch determines that a blocked port should now be the designated or root port because of a topology change, it will go into listening mode and check all BPDUs it receives to make sure that it won’t create a loop once the port goes to forwarding mode.
Convergence
Convergence occurs when all ports on bridges and switches have transitioned to either the forwarding or blocking modes. No data is forwarded until convergence is complete. Before data can be forwarded again, all devices must be updated. Convergence is important to make sure all devices have the same database, but it does cost you some time. It usually takes 50 seconds to go from blocking to forwarding mode, and I don’t recommend changing the default STP timers. (But you can adjust those timers if necessary.) Forward delay means the time it takes to transition a port from listening to learning mode or vice versa.
Spanning Tree Example
It’s time to begin using and not just reading about this stuff. It’s important to see how a spanning tree works in an internetwork, because it will really help you understand it better. So in this section, I’ll give you a chance to observe what you’ve learned as it takes place in a live network.
In Figure 3.1, you can assume that all five switches have the same priority of 32,768. But now study the MAC address of each switch. By looking at the priority and MAC addresses of each device, you should be able to determine the root bridge:
Once you’ve established which switch has got to be the root bridge, look at the figure again and try to figure out which is the root port on each of the switches. (Hint: Root ports are always forwarding ports, which means they will always be in forwarding mode.) Okay, next try to establish which of the ports will be in blocking mode.
FIGURE 3.1 Spanning tree example
Figure .3.2 has the answers for each of the port states for each switch. Since Switch A has the lowest MAC address, and all five switches use the default priority, Switch A gets to be the root bridge. And remember this: A root bridge always has every port in forwarding mode (designated ports).
To determine the root ports on Switch B and Switch C, just follow the connection to the root bridge. Each direct connection to the root bridge will be a root port, so it will become forwarding. On Switches D and E, the ports connected to Switches B and C are Switches D and E’s closest ports to the root bridge (lowest cost), so those ports are root ports and in forwarding mode.
Take another look at the Figure 3.2. Can you tell which of the ports between Switch D and E must be shut down so a network loop doesn’t occur? Let’s work it out: Since the connection from Switches D and E to Switches B and C are root ports, those can’t be shut down. Next, the bridge ID is used to determine designated and nondesignated ports; so, because Switch D has the lowest (best) bridge ID, Switch E’s port to Switch D will become nondesignated (blocking), and Switch D’s connection to Switch E will be designated (forwarding).
FIGURE 3.2 Spanning tree example answers
When should I worry about spanning tree?
Bob, a Senior Network Administrator at Acme Corporation in San Francisco, is concerned about all the new switches his bosses just asked him to install, which will bring the total number of switches in his network to 20. He is concerned about STP and isn’t sure if he should even think about it since it seems to work OK with the few switches he has installed. Bob calls you for advice. What should you tell Bob when he calls?
If you have fewer than six switches in your internetwork and no more than about 100 users in your network, you would usually just let STP do its job and not worry about it. Understand that each network may vary, but with Bob ending up with about 20 switches, he has to think about STP!
But if you have dozens of switches and hundreds of users in your network, then it’s time to pay attention to how STP is running. That’s because if you don’t set the root switch in this larger switched network, your STP may never converge between switches—a nasty situation that could bring your network down.
Setting the timers and root switch are covered in the CCNP: Building Cisco Multilayer Switched Networks

