How to secure a network using ARP
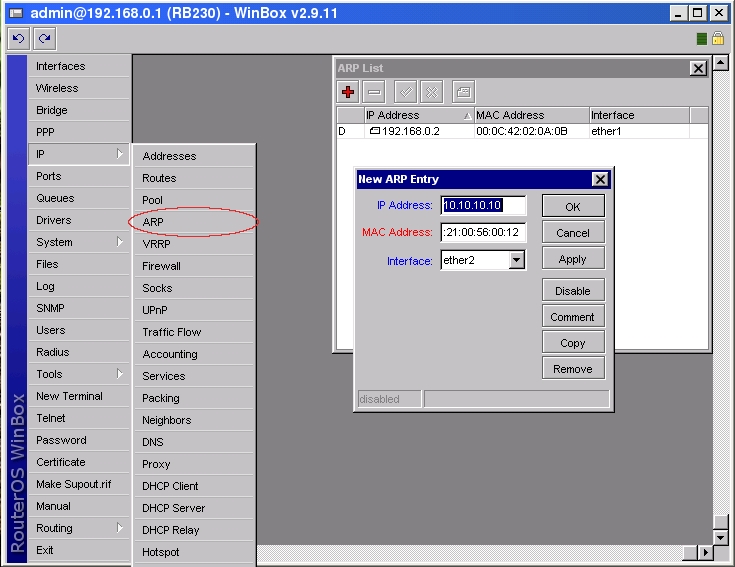
Tuesday, November 27, 2007Although hosts in IP network are addressed using IP addresses, hardware addresses must be used to actually transport data from one host to another at Layer-2 (EG: Ethernet). Address Resolution Protocol (ARP) provides a mapping between the two different forms of addresses. A router has an ARP table that contains ARP entries. ARP entries consist of IP addresses and corresponding hardware addresses (such as a MAC address). Normally ARP provides a dynamic mapping from an IP address to corresponding hardware address by adding ARP entries automatically as they are discovered, but to increase network security static ARP entries can be created manually. By allowing a router to reply only to those static ARP entries found in the ARP table we restrict access to the router and to the network behind the router to only those IP/Hardware address combinations found in the ARP table. To make a router use only static ARP entries follow the steps listed below:
1. Add ARP entries of hosts you want to accept in WinBox
or in Console
[admin@RB230] ip arp> add address=10.10.10.10 interface=ether2 mac-address=06 \
\... 00:21:00:56:00:12
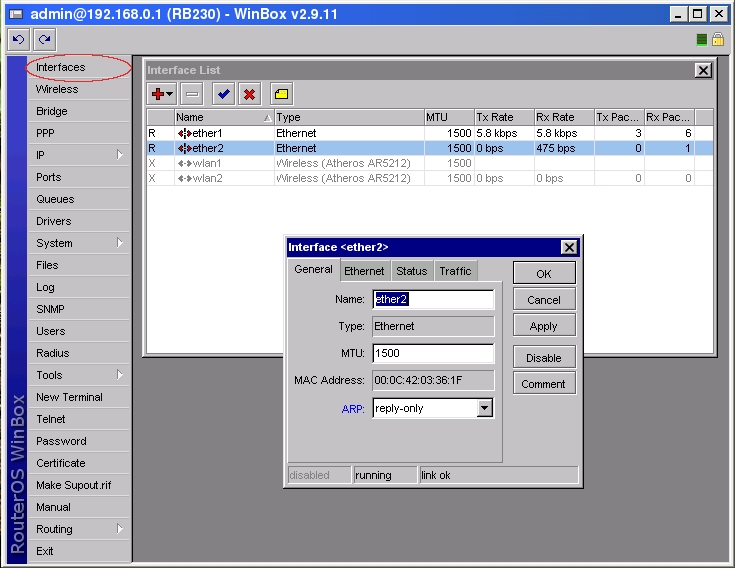
2. Make ether2 interface only reply to ARP requests using your specified ARP entries in WinBox
or in Console
[admin@RB230] > interface ethernet set ether2 arp=reply-only
Drop port scanners
To protect the Router from port scanners, we can record the IPs of hackers who try to scan your box. Using this address list we can drop connection from those IP
in /ip firewall filter
add chain=input protocol=tcp psd=21,3s,3,1 action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="Port scanners to list " disabled=no
Various combinations of TCP flags can also indicate port scanner activity.
add chain=input protocol=tcp tcp-flags=fin,!syn,!rst,!psh,!ack,!urg
action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="NMAP FIN Stealth scan"
add chain=input protocol=tcp tcp-flags=fin,syn
action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="SYN/FIN scan"
add chain=input protocol=tcp tcp-flags=syn,rst
action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="SYN/RST scan"
add chain=input protocol=tcp tcp-flags=fin,psh,urg,!syn,!rst,!ack
action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="FIN/PSH/URG scan"
add chain=input protocol=tcp tcp-flags=fin,syn,rst,psh,ack,urg
action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="ALL/ALL scan"
add chain=input protocol=tcp tcp-flags=!fin,!syn,!rst,!psh,!ack,!urg
action=add-src-to-address-list address-list="port scanners"
address-list-timeout=2w comment="NMAP NULL scan"
Then you can drop those IPs:
add chain=input src-address-list="port scanners" action=drop comment="dropping port scanners" disabled=no
Similarly, you can drop these port scanners in the forward chain, but using the above rules with "chain=forward".
Protecting your customers
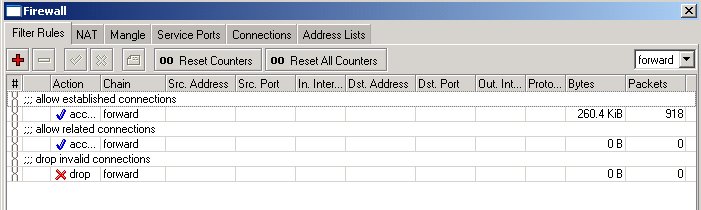
To protect the customer's network, we should check all traffic which goes through router and block unwanted. For icmp, tcp, udp traffic we will create chains, where all unwanted packets will be dropped. For the beginning, we can copy and paste the following commands into RouterOS terminal console:
/ip firewall filter
add chain=forward connection-state=established comment="allow established connections"
add chain=forward connection-state=related comment="allow related connections"
add chain=forward connection-state=invalid action=drop comment="drop invalid connections"
Here, the first two rules deal with packets of already opened or related connections. We assume that those are okay. We do not like invalid connection packets, therefore they are dropped.
Next, we should filter out and drop all unwanted packets that look like coming from virus infected hosts. Instead of adding those rules to the forward chain, we create a new chain for all unwanted netbios and similar traffic. We can give the chain a descriptive name, say, "virus" when adding the following rules to the ip firewall filter (you can copy and paste these rules into the terminal window, if you are in the /ip firewall filter menu):
add chain=virus protocol=tcp dst-port=135-139 action=drop comment="Drop Blaster Worm"
add chain=virus protocol=udp dst-port=135-139 action=drop comment="Drop Messenger Worm"
add chain=virus protocol=tcp dst-port=445 action=drop comment="Drop Blaster Worm"
add chain=virus protocol=udp dst-port=445 action=drop comment="Drop Blaster Worm"
add chain=virus protocol=tcp dst-port=593 action=drop comment="________"
add chain=virus protocol=tcp dst-port=1024-1030 action=drop comment="________"
add chain=virus protocol=tcp dst-port=1080 action=drop comment="Drop MyDoom"
add chain=virus protocol=tcp dst-port=1214 action=drop comment="________"
add chain=virus protocol=tcp dst-port=1363 action=drop comment="ndm requester"
add chain=virus protocol=tcp dst-port=1364 action=drop comment="ndm server"
add chain=virus protocol=tcp dst-port=1368 action=drop comment="screen cast"
add chain=virus protocol=tcp dst-port=1373 action=drop comment="hromgrafx"
add chain=virus protocol=tcp dst-port=1377 action=drop comment="cichlid"
add chain=virus protocol=tcp dst-port=1433-1434 action=drop comment="Worm"
add chain=virus protocol=tcp dst-port=2745 action=drop comment="Bagle Virus"
add chain=virus protocol=tcp dst-port=2283 action=drop comment="Drop Dumaru.Y"
add chain=virus protocol=tcp dst-port=2535 action=drop comment="Drop Beagle"
add chain=virus protocol=tcp dst-port=2745 action=drop comment="Drop Beagle.C-K"
add chain=virus protocol=tcp dst-port=3127-3128 action=drop comment="Drop MyDoom"
add chain=virus protocol=tcp dst-port=3410 action=drop comment="Drop Backdoor OptixPro"
add chain=virus protocol=tcp dst-port=4444 action=drop comment="Worm"
add chain=virus protocol=udp dst-port=4444 action=drop comment="Worm"
add chain=virus protocol=tcp dst-port=5554 action=drop comment="Drop Sasser"
add chain=virus protocol=tcp dst-port=8866 action=drop comment="Drop Beagle.B"
add chain=virus protocol=tcp dst-port=9898 action=drop comment="Drop Dabber.A-B"
add chain=virus protocol=tcp dst-port=10000 action=drop comment="Drop Dumaru.Y"
add chain=virus protocol=tcp dst-port=10080 action=drop comment="Drop MyDoom.B"
add chain=virus protocol=tcp dst-port=12345 action=drop comment="Drop NetBus"
add chain=virus protocol=tcp dst-port=17300 action=drop comment="Drop Kuang2"
add chain=virus protocol=tcp dst-port=27374 action=drop comment="Drop SubSeven"
add chain=virus protocol=tcp dst-port=65506 action=drop comment="Drop PhatBot, Agobot, Gaobot"
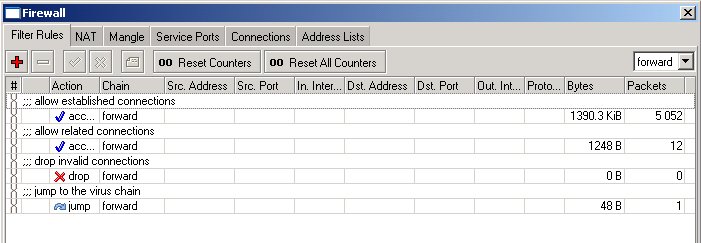
Here, we list all those well known "bad" protocols and ports, used by various trojans and viruses when they take over your computer. This list is incomplete; we should add more rules to it! We can jump to this list from the forward chain by using a rule with action=jump:
add chain=forward action=jump jump-target=virus comment="jump to the virus chain"
The forward chain looks now as follows:
If the packet does not match any of the rules in the virus chain, the processing is returned back to the forward chain. We can simply add rules allowing udp and ping, and then drop everything else (if there are no services on customer's network that need to be accessed from outside):
add chain=forward protocol=icmp comment="allow ping"
add chain=forward protocol=udp comment="allow udp"
add chain=forward action=drop comment="drop everything else"
Securing New RouterOs Router
Securing A Fresh v2.9 RouterOs Device
This document is designed for RouterOs devices that have been cleanly loaded and don’t have any configuration, the configuration outlined in this guide may work for routers already configured but caution must be taken that this configuration does not affect the device.
Please read and understand the entire document before applying this to a device, failure to do so may result in you being unable to access the device
The purpose of this document is to take users though the steps needed to secure access to a RouterOs device while maintaining the ability for other devices to communicate and use certain services. This document works on the idea of 'just-enough' access, that is services or people who need to access the router have 'just-enough' privileges on the router to do their job - and no more. There is no reason for another router that only access's BGP on the device to have full access and likewise a user that log's in to monitor wireless connections should have any write access or the ability to reboot/shutdown etc etc. With this in mind you should look at other areas of your network and asses how they are setup/configured - they may need attention in order to fully secure your network as a whole.
The user's going to pick dancing pigs over security every time. — Bruce Schneier
This is VERY true, the end user and even some sys admin’s I know will choose no security if it means they don’t have to think, some of the things we will put in place on the device will require people using or connecting to the router to do some thing differently, on top of this if a router connecting to the device wants to use a new service on the router you may have enable access.
This can be a pain and sometimes it can go too far, it’s your job to figure out where the balance of security vs. usability is, make it too difficult to do anything and your users won’t will give up, make it too easy to do something and you will be compromised. This may be starting to sound a bit much or too difficult but that’s because we aren’t talking about securing RouterOs now, we are talking about whole network security – security that neither starts nor stops with securing a router.
Having said that lets get into the nuts & bolts of securing RouterOs
Configuring Packages & Hardening Services
Some of you may have started this guide having just loaded RouterOs onto the device which is fine but my personal taste when it comes to packages on RouterOs is to use the roueros-x86/rb500.npk file, why? Because I find it easier to upgrade the router with a single file and its easier when it comes to enabling new services if the router’s role is expanded. There is nothing worse than needing to add a service (I.e. DHCP-Server) to a router running an old RouterOs version and finding you don’t have dhcp-2.9.xx.npk, this is more a problem now that Mikrotik don’t allow you to download old versions from their website anymore.
Installing a new router with routeros-xxx.npk is best done via net-install, if you need to install via CD then your only option is to install from an old version, only install the system package and then upload routeros-xxx.npk via mac-winbox. It’s messy but it’s the only way I have found to do a clean load via CD with the single npk. Once again this is comes down to personal preference and is not required in this document
I always install a router with the following packages enable as a minimum:
- Advanced-Tools
- Ntp
- Security
- System
This installs a basic system where you are able to keep the clock in sync with a external source, a suite of tools enabling advanced monitoring and reporting and allows you to talk to the router securely.
You need to think about the exact role the router will have before you start enabling more packages on the router, if it’s a simple wireless relay station then why would it need DHCP enabled? If the router is to be a Ethernet based firewall then why does it need the wireless enabled. Only enable packages the router need to do its job, remember its all about ‘just-enough’ security
Once you have your router loaded up with only the packages it need’s its time to look at the services that are running by default.
By default you can access the router by:
- Telnet
- SSH
- HTTP
- Winbox
- FTP
- Mac-Telnet
Later in the document we will be adding a firewall to control access to the above services but right now you may choose that some services you just wont use ever, on my routers I choose disable all services but Mac-Telnet, Winbox and SSH. All other services I have no need for and disable them. Disabling a service is easy
/ip services print
Will return this on a default load of routeros
Flags: X - disabled, I - invalid
# NAME PORT ADDRESS CERTIFICATE
0 telnet 23 0.0.0.0/0
1 ftp 21 0.0.0.0/0
2 www 80 0.0.0.0/0
3 ssh 22 0.0.0.0/0
4 X www-ssl 443 0.0.0.0/0 none
To disable a service is simple
/ip service disable
Once you have configured the services to your liking it's time to look at other ways to interface with the router, first up is SNMP which is used by a lot of programs to monitor devices (I.e. The Dude)
SNMP is disabled by default and if you have other means of monitoring devices it is safe to leave disabled. I prefer to use The Dude to monitor my network so I will go ahead and enable access and set some helpful fields
/snmp set enabled=yes location=”The Matrix” contact=neo@zion.org
SNMP in RouterOs 2.9 is read only, so the only danger from enabling access to it is that without firewalling to stop access anyone on your network or the rest of the world if the router has a public IP address will be able to look at Wireless signal levels etc.
Now that your router has some basic hardening its time to look at user’s who access the router and the privileges that they have
Users & Passwords
By default your router has 1 user, admin, which has no password set. With RouterOs if you set password for the admin user, add no other users with write/password privileges and forget the password there is ‘’’’’NO’’’’’ way to log in or recover the password, you must do a reinstall.
Before going any further you should check to see if the company you are working has a policy on user’s and passwords.
If your company does have a policy on this you must check to see if this document conflicts with it
If it does seek approval before implementing this document any further
The first thing we will do is give the default admin a password. In my network all user passwords are 32 characters long, I use a password generator here which will create 10 passwords at a time, if you need more just hit refresh and it generate more passwords
/user set admin password=putpasshere
Once you do this its best to exit and reconnect Winbox.
Next up is adding a fail-safe user, this is a user with admin rights and a simple password that is ‘’’’’only’’’’’ allowed to connect from the local terminal. The purpose of this is to prevent you from have to reinstall the router in the event you lose the admin password. I use a simple password such as my driver license number of IRD number as the password, it’s critical that the password is not something you will forget or lose. In my country your drivers license and IRD number are set for life and make for perfect backup user passwords.
In reality I don’t use my driver license or IRD number, I use another document that is just as easy to remember, don’t use something that is easy to get a hold of. If you lose your wallet the last you want to be doing is changing all your router’s passwords.
So lets add this user
/user add name=badmin password=putpasshere group=full address=127.0.0.1/32
At this point your router is password protected and has a fail-safe in case you lose the big password. You may need to add more users for monitoring etc, don’t hand out the admin password to everyone. If someone needs access to the router determine what privileges they need and create a user for them. The rest of this document is useless to you if you don’t keep the usernames and password secure
‘’Amateurs hack systems, professionals hack people.’’ — ‘’’Bruce Schneier’’’
[edit] Port Knocking
In the firewall we will load onto the router in the next section we divide up access into 2 sections
- An address list of devices that have full access to the router
- All other devices that have limited access to the router
One thing that all other devices are limited to is they have no Winbox/SSH/telnet access to the router, which sometimes will mean you can't get into it. One way to temporarily allow full access to a router is port knocking.
Port knocking with RouterOs is a way of adding a dynamic IP address into an address list for a specified amount of time. The way it works is like this
- Client sends packet to router on port 1337
- Router adds client’s IP address to address list “temp” with a timeout of 15 seconds
- Client sends packer to router on port 7331
- Router checks to see if the client’s IP address is on address list “temp”
- If it is then router adds IP address to address list “safe” with a timeout of 15 minutes
- Client has full access to router for 15 minutes
This feature is completely customisable with you able to define how many ports the client has to ‘knock’ before its given access, you can define what port numbers and what protocols you must knock and the timeout values.
A windows knocking client is available here and is used like so
Knock.exeport:protocol port:protocol port:protocol…
So to gain access to the router in the example above we would run
Knock.exe 192.168.0.2 1337:tcp 7331:tcp
While this feature is useful it is another weak point in security, in the firewall rules I show which rules are used to create a port knock, if you leave these rules out there will be no port knocking on the router
Loading A Firewall
Next up is loading up a firewall, right now you router is secure from access by passwords, but passwords are one layer of security – not the only layer. This script is based on the firewall used on the MT demo router but has a few changes to it, it only protects the router and contains no ‘forward’ firewall rules
/ ip firewall filter
add chain=input protocol=tcp dst-port=1337 action=add-src-to-address-list address-list=knock \
address-list-timeout=15s comment="" disabled=no
add chain=input protocol=tcp dst-port=7331 src-address-list=knock action= add-src-to-address-list \
address-list=safe address-list-timeout=15m comment="" disabled=no
These rules setup port knocking, it set’s up the example we used above and will add the IP address to the ‘safe’ address-list, this is the address-list used in this firewall to permit full unrestricted access to the router
add chain=input connection-state=established action=accept comment="accept established connection packets" disabled=no
add chain=input connection-state=related action=accept comment="accept related connection packets" disabled=no
add chain=input connection-state=invalid action=drop comment="drop invalid packets" disabled=no
These rules make sure only valid connections are going to the router and will drop any that are invalid.
add chain=input src-address-listddress-list=safe action=accept comment="Allow access to router from known network" disabled=no
This rule is the rule that allows full access to the router for certain IP addresses, This list contains static entries for IP’s you want to always have access and also contains the dynamic IP’s of those added by port knocking if used
add chain=input protocol=tcp psd=21,3s,3,1 action=drop comment="detect and drop port scan connections" disabled=no
add chain=input protocol=tcp connection-limit=3,32 src-address-list=black_list action=tarpit \
comment="suppress DoS attack" disabled=no
add chain=input protocol=tcp connection-limit=10,32 action= add-src-to-address-list \
address-list=black_list address-list-timeout=1d comment="detect DoS attack" disabled=no
These rule’s are a little reactive to DoS and port scanning attempts, port scanning is dropped but a DoS attack is ‘tarpitted’ in that all connection’s are slowed down to increase the resource usage on the attackers device
add chain=input protocol=icmp action=jump jump-target=ICMP comment="jump to chain ICMP" disabled=no
add chain=input action=jump jump-target=services comment="jump to chain services" disabled=no
These 2 rules jump to chains we are about to create, jumping is handy because it allows you to reuse the same rule in different chains (I.e. Input and Forward can jump to the same chain and run the same rules)
add chain=input dst- address-type=broadcast action=accept comment="Allow Broadcast Traffic" disabled=no
Allow Broadcast traffic to the router, this is needed sometimes by things like NTP
add chain=input action=log log-prefix="Filter:" comment="" disabled=no
add chain=input action=drop comment="drop everything else" disabled=no
And this is the rule that deny’s all access to the router, if traffic hasn’t been accepted by once of the rules above then it will be dropped
add chain=ICMP protocol=icmp icmp-options=0:0-255 limit=5,5 action=accept comment="0:0 and limit for 5pac/s" disabled=no
add chain=ICMP protocol=icmp icmp-options=3:3 limit=5,5 action=accept comment="3:3 and limit for 5pac/s" disabled=no
add chain=ICMP protocol=icmp icmp-options=3:4 limit=5,5 action=accept comment="3:4 and limit for 5pac/s" disabled=no
add chain=ICMP protocol=icmp icmp-options=8:0-255 limit=5,5 action=accept comment="8:0 and limit for 5pac/s" disabled=no
add chain=ICMP protocol=icmp icmp-options=11:0-255 limit=5,5 action=accept comment="11:0 and limit for 5pac/s" disabled=no
add chain=ICMP protocol=icmp action=drop comment="Drop everything else" disabled=no
These rules form the ‘ICMP’ chain which we jumped to from input, it limited various ICMP packet to stop people ping flooding you
add chain=services src-address-listddress=127.0.0.1 dst- address=127.0.0.1 action=accept comment="accept localhost" disabled=no
add chain=services protocol=udp dst-port=20561 action=accept comment="allow MACwinbox " disabled=no
add chain=services protocol=tcp dst-port=2000 action=accept comment="Bandwidth server" disabled=no
add chain=services protocol=udp dst-port=5678 action=accept comment=" MT Discovery Protocol" disabled=no
add chain=services protocol=tcp dst-port=161 action=accept comment="allow SNMP" disabled=yes
add chain=services protocol=tcp dst-port=179 action=accept comment="Allow BGP" disabled=yes
add chain=services protocol=udp dst-port=5000-5100 action=accept comment="allow BGP" disabled=yes
add chain=services protocol=udp dst-port=123 action=accept comment="Allow NTP" disabled=yes
add chain=services protocol=tcp dst-port=1723 action=accept comment="Allow PPTP" disabled=yes
add chain=services protocol=gre action=accept comment="allow PPTP and EoIP" disabled=yes
add chain=services protocol=tcp dst-port=53 action=accept comment="allow DNS request" disabled=yes
add chain=services protocol=udp dst-port=53 action=accept comment="Allow DNS request" disabled=yes
add chain=services protocol=udp dst-port=1900 action=accept comment="UPnP" disabled=yes
add chain=services protocol=tcp dst-port=2828 action=accept comment="UPnP" disabled=yes
add chain=services protocol=udp dst-port=67-68 action=accept comment="allow DHCP" disabled=yes
add chain=services protocol=tcp dst-port=8080 action=accept comment="allow Web Proxy" disabled=yes
add chain=services protocol=ipencap action=accept comment="allow IPIP" disabled=yes
add chain=services protocol=tcp dst-port=443 action=accept comment="allow https for Hotspot" disabled=yes
add chain=services protocol=tcp dst-port=1080 action=accept comment="allow Socks for Hotspot" disabled=yes
add chain=services protocol=udp dst-port=500 action=accept comment="allow IPSec connections" disabled=yes
add chain=services protocol=ipsec-esp action=accept comment="allow IPSec" disabled=yes
add chain=services protocol=ipsec-ah action=accept comment="allow IPSec" disabled=yes
add chain=services protocol=udp dst-port=520-521 action=accept comment="allow RIP" disabled=yes
add chain=services protocol=ospf action=accept comment="allow OSPF" disabled=yes
add chain=services action=return comment="" disabled=no
These are the services that we allow ANYone to access, as you can see I’ve disabled most of them by default. The only ones enabled are services I personally feel should always be accessible
- Mac-Telnet
- Bandwidth Test Server
- MT Discovery
All other services should only be enabled if they need to be, running this script on a production router already configured will cause it to drop IPSec, BGP, EOIP and a bunch of other services so I must repeat myself again
Don’t apply this firewall on a production router unmodified – it will break some services
Logging & Syslog
So you’ve got long passwords and a firewall that limit’s access to your router. Everything’s great, you see the “Drop Everything Else” counter rising and you check the logs on the router to make sure nobody’s got in. Trouble is you’re now assuming that the data on your router is accurate and hasn’t been fiddled with, someone could have gotten in somehow, is altering your network and you don’t have a clue because they altered the logs or their access has gone beyond the 100 line storage default of RouterOs logging.
Got you worried yet? I should have, when someone compromises any device on your network you can no longer assume the data it holds is clean. You must assume that everything on that device has been altered or removed. On RouterOs it’s actually very difficult to remove entries in the log without erasing the entire log by default but its not impossible, nothing ever is. We are about to go through RouterOs and change what’s logged and where its logged to, in order to be able to accurately tell what’s going on in your router you need to log some information about changes and login attempts to an outside device
By default RouterOs has the following logging setup
/system logging print
Flags: X - disabled, I - invalid
# TOPICS ACTION PREFIX
0 info memory
1 error memory
2 warning memory
3 critical echo
Which is really bad because if your router suffers a power outage or random reboot you lose all log’s. So the first thing we are going to do is log some things to disk.
Erase all the current logging rules
/system logging print
/system logging remove 0
/system logging remove 1
/system logging remove 2
/system logging remove 3
Setup logging to log some things to disk
/system logging add topics=critical action=disk
/system logging add topics=critical action=echo
/system logging add topics=error action=disk
/system logging add topics=warning action=disk
/system logging add topics=info action=memory
Now the next trouble is that by default RouterOs will only store that last 100 lines in memory or on disk. Depending on the amount of ram and free disk space you should up this, personally I set this to 300 lines in memory and disk for RouterBoards and 1000 for PC routers. You can do this by the following command
/system logging action print
/system logging action set 0 disk-lines=XXX
/system logging action set 1 disk-lines=XXX
Now the router will log something’s to disk, others to memory and you will be able to look back further in the logs on the router
If you look back to the firewall script we put in place you will notice that we set it up to log all the dropped input packets, right now you will see them in memory as they are logged under ‘info’ what we will do now is create another file on the disk to store the firewall hits and alter the logging rules so they get logged to disk but don’t clog up the memory
First we setup the new target
/system logging action add target=disk disk-lines=XXX name=FirewallHits
Then we alter the logging actions to stop the firewall clogging up the log
/system logging print
/system logging set 0 topics=info,!firewall
And now we set it so all the firewall hits get sent to the new target
/system logging add topics=firewall action=FirewallHits
And done, now all the hits your firewall get will be logged to the disk and will no longer clog up your main log files, the last thing left to do with logging is log everything to a remote source, for this you will need a remote server running either windows or *NIX with a Syslog daemon running. I wont go through setting up a Syslog daemon as this is extremely platform specific however it is simple to setup a catchall Syslog daemon.
RouterOs has a built in logging action called ‘remote’ all that you need to do is specify the destination IP address where Syslog is running, we can do this by issuing the following commands
/system logging action print
/system logging action set 3 remote=192.168.0.3:514
Remember to add ‘:514’ to the end of the IP address as this specifies which port to use. Once we have set the IP we can go ahead and add a rule to log everything to the daemon
/system logging add action=remote topics=info,warning,critical,firewall,error prefix="RouterId"
Change the prefix to something that identifies your router and your all done.
With this logging setup in place you are in a better position to know what’s going on in your network and to know that the information you are reading is correct, remember when in doubt check the remote Syslog.
Another thing to remember is that all of this logging setup is useless if you never look at it, get into a routine of looking at the log files everyday. Setting up some advanced traps on your remote Syslog to filter some of the rubbish may make this easier
Under *nix-like OS you should do that (FreeBSD, for example):
1. vi /etc/rc.conf and typed lines below.
syslogd_enable="YES" # Run syslog daemon (or NO).
syslogd_program="/usr/sbin/syslogd" # path to syslogd, if you want a different o
syslogd_flags="" # Flags to syslogd (if enabled).
By default into "syslogd_flags" set "-s" option. Don't forget remove it. The "-a" options are ignored if the "-s" option is also specified. See man syslogd.
2. vi /etc/syslog.conf and typed next:
+@
# syslog settings of current system
+*
#
+
*.* /var/log/mikrotik.log
+*
3. /etc/rc.d/syslogd restart.
It's all.
NTP Sync & Misc.
Time, it’s a funny thing. You may not be aware that your device is running on the wrong time, this can be a real pain when you’re faced with an intrusion and reading the logs you discover they are all out by a few hours. It makes it difficult when your cross checking firewall hits against another device and you have to keep adjusting all the results by a few hours. Also if you place firewall rules or simple queues in place that work only at specific times you will find they will work at strange times
One way of correct this is by use of an external time source via NTP. You can find a list of NTP servers in your region here. Because the RouterOs NTP client works on IP’s directly rather than doing a DNS lookup each time you must enter the NTP server’s in as IP addresses
Before setting up the NTP client you need to make sure your time zone is correct
/system clock set time-zone=+12
Once that’s done you can setup your NTP client
/system ntp client set enabled=yes primary-ntp=192.168.0.2 secondary-ntp=192.168.0.3 mode=unicast
It’s as simple as that! Now you router should always be telling the correct time
Throughout this document I have pushed you to think about security of the entire network even tho this document is for securing a single router. My reasons for this are simple, security is like a chain, we have just secured 1 link in that chain but this is pointless if the link before or after is weak or insecure. You need to look at how you keep your network secure, some questions you might want to ask yourself
- Who has access to our passwords?
- Who has physical access to our hardware?
- Do I know what every device on our network is?
- How can I tell if a new device pops up on our network?
- How long would it take me to notice if a router’s password changed?
There are a lot more questions you should be asking but these should get your thinking. Finally security is not a product nor is it a set of firewall rules and it’s not a 1 time thing either. Good security is an on-going area of managing your network that is often overlooked or neglected, until you are compromised and then you’re under the microscope
Last Words
इ hope you find this useful and not a waste of your time, I like feedback about what I write so feel free to leave some on the talk page Talk:Securing_New_RouterOs_Router These guides aren’t perfect so if you see a flaw or error please feel free to update it and let me know via the talk page
Securing your router
Change admin's password
Just select the Password menu within the winbox GUI, for example:
Or, type the following command in the CLI:
[admin@MikroTik] > / password
old password:
new password: ******
retype new password: ******
This will change your current admin's password to what you have entered twice. Make sure you remember the password! If you forget it, there is no recovery. You need to reinstall the router!
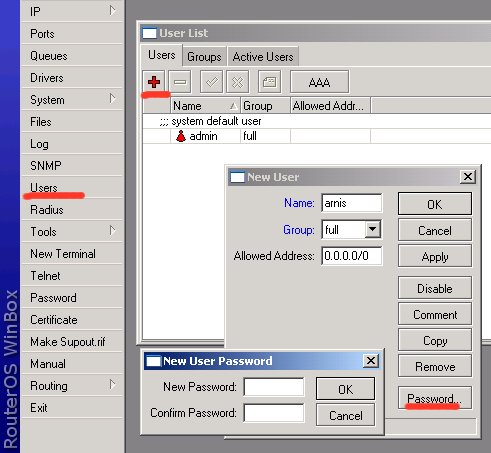
Add users to the system
You should add each user that is going to log on to the router as a separate user and specify group of privileges. Add yourself as user of group full (same as for admin), for example:
You may create new groups for users with specific tasks.
Set up packet filtering
All packets with destination to the router are processed against the ip firewall filter's input chain. Note, that the input chain does not affect packets which are being transferred through the router!
You can add following rules to the input chain under /ip firewall filter (just 'copy and paste' to the router using Terminal Console or configure the relevant arguments in WinBox):
/ ip firewall filter
add chain=input connection-state=established comment="Accept established connections"
add chain=input connection-state=related comment="Accept related connections"
add chain=input connection-state=invalid action=drop comment="Drop invalid connections"
add chain=input protocol=udp action=accept comment="UDP" disabled=no
add chain=input protocol=icmp limit=50/5s,2 comment="Allow limited pings"
add chain=input protocol=icmp action=drop comment="Drop excess pings"
add chain=input protocol=tcp dst-port=22 comment="SSH for secure shell"
add chain=input protocol=tcp dst-port=8291 comment="winbox"
# Edit these rules to reflect your actual IP addresses! #
add chain=input src-address=159.148.172.192/28 comment="From Mikrotikls network"
add chain=input src-address=10.0.0.0/8 comment="From our private LAN"
# End of Edit #
add chain=input action=log log-prefix="DROP INPUT" comment="Log everything else"
add chain=input action=drop comment="Drop everything else"
Use /ip firewall filter print input stats command to see how many packets have been processed against these rules. Use reset-counters-all command to reset the counters. Examine the system log file /log print to see the packets which have been dropped.
You may need to include additional rules to allow access from certain hosts, etc. Remember that firewall rules are processed in the order they appear on the list! After a rule matches the packet, no more rules are processed for it. After adding new rules, move them up using the move command.
Note, if you mis-configured the firewall and have locked yourselves out from the router, you may use MAC telnet from another router or workstation on the same LAN to connect to your router and correct the problem.
Limit Different Bandwidth In Day and Night
Limit Different Bandwidth In Day and Night.
There are lot many ways to limit bandwidth for day and Night, but personally I found this is the easiest way, Here it is.
I have used Simple Queue, Script and Scheduler.
Suppose we have one network 192.168.1.0/24 and want to limit Bandwidth for day and Night Time.
Network 192.168.1.0/24
Bandwidth = 06:00am – 18:00pm – 1Mbps.
Bandwidth = 18:00pm – 06:00am – 2Mbps.
Create two simple queues for the same network with different Bandwidth Limit.
/queue simple
#name=”Day” target-addresses=192.168.1.0/24 dst-address=0.0.0.0/0
interface=parent=none direction=both priority=8
queue=default-small/default-small limit-at=512k/512k
max-limit=1M/1M total-queue=default-small
#name=”Night” target-addresses=192.168.1.0/24 dst-address=0.0.0.0/0
interface=parent=none direction=both priority=8
queue=default-small/default-small limit-at=1M/1M
max-limit=2M/2M total-queue=default-small
Now, write scripts
/system script
#name=”Day” source=/queue simple enable Day; /queue simple disable Night
#name=”Night” source=/queue simple enable Night; /queue simple disable Day
Finally, Schedule it
/system scheduler
#name=”Day” on-event=Day start-date=oct/13/2007 start-time=06:00:00 interval=1d
#name=”Night” on-event=Night start-date=oct/13/2007 start-time=18:00:00 interval=1d
Queue Tree with more than two interfaces
Basic Setup
This page will tak about how to make QUEUE TREE in RouterOS that with Masquerading for more than two interfaces. It's for sharing internet connection among users on each interfacess. In manual this possibility isn't writted.
First, let's set the basic setting first. I'm using a machine with 3 or more network interfaces:
[admin@instaler] > in pr
# NAME TYPE RX-RATE TX-RATE MTU
0 R public ether 0 0 1500
1 R wifi1 wlan 0 0 1500
2 R wifi2 wlan 0 0 1500
3 R wifi3 wlan 0 0 1500
And this is the IP Addresses for each interface:
[admin@instaler] > ip ad pr
Flags: X - disabled, I - invalid, D - dynamic
# ADDRESS NETWORK BROADCAST INTERFACE
0 10.20.1.0/24 10.20.1.0 10.20.1.255 public
1 10.10.2.0/24 10.10.2.0 10.10.2.255 wifi1
2 10.10.3.0/24 10.10.3.0 10.10.3.255 wifi2
3 10.10.4.0/24 10.10.4.0 10.10.4.255 wifi3
On the public you can add NAT or proxy if you want.
Mangle Setup
And now is the most important part in this case.
We need to mark our users. One connection for upload and second for download. In this example I add mangle for one user. At the end I add mangle for local transmission because I don't QoS local trafic emong users. But for user I need to separate upload and download.
[admin@instaler] ip firewall mangle> print
Flags: X - disabled, I - invalid, D - dynamic
disabled=no
0 chain=forward src-address=10.10.2.36 action=mark-connection \
new-connection-mark=users-userU passthrough=yes comment="" disabled=no
1 chain=forward dst-address=10.10.2.36 action=mark-connection \
new-connection-mark=users-userD passthrough=yes comment="" disabled=no
2 chain=forward connection-mark=users-userU action=mark-packet \
new-packet-mark=userU passthrough=yes comment="" disabled=no
3 chain=forward connection-mark=users-userD action=mark-packet \
new-packet-mark=userD passthrough=yes comment="" disabled=no
98 chain=forward src-address=10.10.0.0/16 dst-address=10.10.0.0/16
action=mark-connection new-connection-mark=users-lokal passthrough=yes
99 chain=forward connection-mark=users-lokal action=mark-packet
new-packet-mark=lokalTrafic passthrough=yes
Queue Tree Setup
And now, the queue tree setting. We need one rule for downlink and one rule for uplink. Be careful when choosing the parent. for downlink traffic, we use parent "global-out", because we have two or more downloading interfaces. And for uplink, we are using parent "public", we want QoS uplink traffic. (I'm using pcq-up and download from manual) This example is for 2Mb/1Mb
[admin@instaler] > queue tree pr
Flags: X - disabled, I - invalid
0 name="Download" parent=global-out packet-mark="" limit-at=0
queue=pcq-download priority=1 max-limit=2000000 burst-limit=0
burst-threshold=0 burst-time=0s
1 name="Upload" parent=WGW packet-mark="" limit-at=0 queue=pcq-upload
priority=1 max-limit=1000000 burst-limit=0 burst-threshold=0
burst-time=0s
Now we add our user:
2 name="user10D" parent=Download packet-mark=userD limit-at=0
queue=pcq-download priority=5 max-limit=0 burst-limit=0
burst-threshold=0 burst-time=0s
3 name="user10U" parent=Upload packet-mark=userU limit-at=0
queue=pcq-upload priority=5 max-limit=0 burst-limit=0 burst-threshold=0
burst-time=०स्
source = http://wiki.mikrotik.com
Queue with Masquerading and Internal Web-Proxy
Introduction
This page will tak about how to make QUEUE TREE in RouterOS that also running Web-Proxy and Masquerading. Several topics in forum say it's impossible to do.
In version 2.9.x, we can not know which traffic is HIT and which traffic is MISS from web-proxy. Several people want to make a configuration, to let cache data in proxy (HIT traffic) deliver in maximum possible speed. In other word, if we already have the requested data, those process will not queued.
In ver 3.0 we can do this, using TOS header modification in web-proxy feature. We can set any TOS value for the HIT traffic, and make it as parameter in mangle.
Basic Setup
First, let's set the basic setting first. I'm using a machine with 2 network interface:
admin@instaler] > in pr
# NAME TYPE RX-RATE TX-RATE MTU
0 R public ether 0 0 1500
1 R lan wlan 0 0 1500
And this is the IP Address for each interface:
[admin@instaler] > ip ad pr
Flags: X - disabled, I - invalid, D - dynamic
# ADDRESS NETWORK BROADCAST INTERFACE
0 192.168.0.217/24 192.168.0.0 192.168.0.255 public
1 172.21.1.1/24 172.21.1.0 172.21.1.255 lan
Don't forget to set the transparant web-proxy. We set cache-hit-dscp: 4.
[admin@instaler] > ip proxy pr
enabled: yes
src-address: 0.0.0.0
port: 3128
parent-proxy: 0.0.0.0
parent-proxy-port: 0
cache-drive: system
cache-administrator: "webmaster"
max-cache-size: none
cache-on-disk: yes
maximal-client-connections: 600
maximal-server-connections: 600
max-fresh-time: 3d
serialize-connections: yes
cache-hit-dscp: 4
Firewall NAT
Make 2 NAT rules, 1 for Masquerading, and the other for redirecting transparant proxy.
[admin@instaler] ip firewall nat> pr
Flags: X - disabled, I - invalid, D - dynamic
0 chain=srcnat out-interface=public
src-address=172.21.1.0/24 action=masquerade
1 chain=dstnat in-interface=lan src-address=172.21.1.0/24
protocol=tcp dst-port=80 action=redirect to-ports=3128
Mangle Setup
And now is the most important part in this case.
If we want to make HIT traffic from web proxy not queued, we have to make a mangle to handle this traffic. Put this rule on the beginning of the mangle, as it will check first.
[admin@instaler] > ip firewall mangle print
Flags: X - disabled, I - invalid, D - dynamic
0 ;;; HIT TRAFFIC FROM PROXY
chain=output out-interface=lan
dscp=4 action=mark-packet
new-packet-mark=proxy-hit passthrough=no
As we will make Queue for uplink and downlink traffic, we need 2 packet-mark. In this example, we use "test-up" for uplink traffic, and "test-down" for downlink traffic.
For uplink traffic, it's quite simple. We need only one rule, using SRC-ADDRESS and IN-INTERFACE parameters, and using PREROUTING chain. Rule number #1.
But for downlink, we have to make sevaral rules. As we use masquerading, we need Connection Mark, named as "test-conn". Rule no #2.
Then we have to make 2 more rules. First rule is for non-HTTP connection / direct connection. We use chain forward, as the data traveling through the router. Rule no #3.
The second rule is for data coming from web-proxy to the client (MISS traffic). We use OUTPUT chain, as the data coming from internal process in the router itself. Rule no #4.
For both rules (no #3 and #4) we named it "test-down".
Please be aware, we use passthrough only for connection mark (rule no #2).
[admin@instaler] > ip firewall mangle print
Flags: X - disabled, I - invalid, D - dynamic
1 ;;; UP TRAFFIC
chain=prerouting in-interface=lan
src-address=172.21.1.0/24 action=mark-packet
new-packet-mark=test-up passthrough=no
2 ;;; CONN-MARK
chain=forward src-address=172.21.1.0/24
action=mark-connection
new-connection-mark=test-conn passthrough=yes
3 ;;; DOWN-DIRECT CONNECTION
chain=forward in-interface=public
connection-mark=test-conn action=mark-packet
new-packet-mark=test-down passthrough=no
4 ;;; DOWN-VIA PROXY
chain=output out-interface=lan
dst-address=172.21.1.0/24 action=mark-packet
new-packet-mark=test-down passthrough=no
Queue Tree Setup
And now, the queue tree setting. We need one rule for downlink and one rule for uplink. Be careful when choosing the parent. for downlink traffic, we use parent "lan", the interface name for local network. And for uplink, we are using parent "global-in".
[admin@instaler] > queue tree pr
Flags: X - disabled, I - invalid
0 name="downstream" parent=lan packet-mark=test-down
limit-at=32000 queue=default priority=8
max-limit=32000 burst-limit=0
burst-threshold=0 burst-time=0s
1 name="upstream" parent=global-in
packet-mark=test-up limit-at=32000
queue=default priority=8
max-limit=32000 burst-limit=0
burst-threshold=0 burst-time=0s
You can use those mangle also with PCQ।
source = http://wiki.mikrotik.com
Different limits for Local/Overseas traffic for 3 bandwitch rates using pcq and queue tree
1. Introdution
Let's consider the scenario, when you want to apply different limits for many users to Local and Oversea traffic and don`t want load cpu with a lot of simple queues and you want sell for customers 3 bandwitch rates.
1.12/6 Mbps Latvian Traffic 1Mbps/512Kbps Overseas traffic
2.6/3 Mbps Latvian Traffic 512kbps/256Kbps Overseas traffic
3.4/2 Mbps Latvian Traffic 256Kbps/128Kbps Overseas traffic
Queue trees will limit data rate for the Local country traffic and Oversea traffic In this scenario local country is Latvia. List of all Latvian subnets located at http://www.nic.lv/local.net
2. Configuration
/ ip firewall address-list
add list=12/6 address=192.168.0.2 comment="12/6mbps Local traffic 1mbps/512kbps oversea"
add list=6/3 address=192.168.0.3 comment="6/3mbps Local traffic 512kbps/256kbps oversea"
add list=4/2 address=192.168.0.4 comment="4/2mbps Local traffic 256kbps/128kbps oversea"
add list=Latvia address=159.148.0.0/16 comment="" disabled=no
add list=Latvia address=193.41.195.0/24 comment="" disabled=no
add list=Latvia address=193.41.33.0/24 comment="" disabled=no
add list=Latvia address=193.41.45.0/24 comment="" disabled=no
add list=Latvia address=193.68.64.0/19 comment="" disabled=no
add list=Latvia address=193.108.29.0/24 comment="" disabled=no
add list=Latvia address=193.108.144.0/22 comment="" disabled=no
add list=Latvia address=193.108.185.0/24 comment="" disabled=no
/ ip firewall mangle
add chain=forward action=mark-packet new-packet-mark=LV_DL_6M passthrough=yes \
in-interface=public src-address-list=latvia comment="Default mangle for \
Latvia Download" disabled=no
add chain=forward action=mark-packet new-packet-mark=LV_UL_3M passthrough=yes \
in-interface=local dst-address-list=latvia comment="Default mangle for \
Latvia Upload" disabled=no
add chain=forward action=mark-packet new-packet-mark=OS_DL_512k \
passthrough=yes in-interface=public src-address-list=!latvia \
comment="Default mangle for Oversea Download" disabled=no
add chain=forward action=mark-packet new-packet-mark=OS_UL_256k \
passthrough=yes in-interface=local dst-address-list=!latvia \
comment="Default mangle for Oversea Upload" disabled=no
add chain=forward action=mark-packet new-packet-mark=LV_DL_12M passthrough=no \
in-interface=public src-address-list=latvia dst-address-list=12/6 \
comment="Tarif 12/6 Latvia Download" disabled=no
add chain=forward action=mark-packet new-packet-mark=LV_UL_6M passthrough=no \
in-interface=local src-address-list=12/6 dst-address-list=latvia \
comment="Tarif 12/6 Latvia Upload" disabled=no
add chain=forward action=mark-packet new-packet-mark=OS_DL_1M passthrough=no \
in-interface=public src-address-list=!latvia dst-address-list=12/6 \
comment="Tarif 12/6 Oversea Download" disabled=no
add chain=forward action=mark-packet new-packet-mark=OS_UL_512k passthrough=no \
in-interface=local src-address-list=12/6 dst-address-list=!latvia \
comment="Tarif 12/6 Oversea Upload" disabled=no
add chain=forward action=mark-packet new-packet-mark=LV_DL_4M passthrough=no \
in-interface=public src-address-list=latvia dst-address-list=4/2 \
comment="Tarif 4/2 Latvia Download" disabled=no
add chain=forward action=mark-packet new-packet-mark=LV_UL_2M passthrough=no \
in-interface=local src-address-list=4/2 dst-address-list=latvia \
comment="Tarif 4/2 Latvia Upload" disabled=no
add chain=forward action=mark-packet new-packet-mark=OS_DL_256k passthrough=no \
in-interface=public src-address-list=!latvia dst-address-list=4/2 \
comment="Tarif 4/2 Oversea Download" disabled=no
add chain=forward action=mark-packet new-packet-mark=OS_UL_128k passthrough=no \
in-interface=local src-address-list=4/2 dst-address-list=!latvia \
comment="Tarif 4/2 Oversea Upload" disabled=no
/ queue type
add name="LV_DL_12M" kind=pcq pcq-rate=12000000 pcq-limit=50 \
pcq-classifier=dst-address pcq-total-limit=2000
add name="LV_DL_6M" kind=pcq pcq-rate=6000000 pcq-limit=50 \
pcq-classifier=dst-address pcq-total-limit=2000
add name="LV_DL_4M" kind=pcq pcq-rate=4000000 pcq-limit=50 \
pcq-classifier=dst-address pcq-total-limit=2000
add name="LV_UL_6M" kind=pcq pcq-rate=6000000 pcq-limit=50 \
pcq-classifier=src-address pcq-total-limit=2000
add name="LV_UL_3M" kind=pcq pcq-rate=3000000 pcq-limit=50 \
pcq-classifier=src-address pcq-total-limit=2000
add name="LV_UL_2M" kind=pcq pcq-rate=2000000 pcq-limit=50 \
pcq-classifier=src-address pcq-total-limit=2000
add name="OS_DL_1M" kind=pcq pcq-rate=1000000 pcq-limit=50 \
pcq-classifier=dst-address pcq-total-limit=2000
add name="OS_DL_512k" kind=pcq pcq-rate=512000 pcq-limit=50 \
pcq-classifier=dst-address pcq-total-limit=2000
add name="OS_DL_256k" kind=pcq pcq-rate=256000 pcq-limit=50 \
pcq-classifier=dst-address pcq-total-limit=2000
add name="OS_UL_512k" kind=pcq pcq-rate=512000 pcq-limit=50 \
pcq-classifier=src-address pcq-total-limit=2000
add name="OS_UL_256k" kind=pcq pcq-rate=256000 pcq-limit=50 \
pcq-classifier=src-address pcq-total-limit=2000
add name="OS_UL_128k" kind=pcq pcq-rate=128000 pcq-limit=50 \
pcq-classifier=src-address pcq-total-limit=2000
/ queue tree
add name="LV_DL_12M" parent=local packet-mark=LV_DL_12M limit-at=0 queue=LV_DL_12M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="LV_DL_6M" parent=local packet-mark=LV_DL_6M limit-at=0 queue=LV_DL_6M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="LV_UL_2M" parent=public packet-mark=LV_UL_2M limit-at=0 queue=LV_UL_2M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="LV_DL_4M" parent=local packet-mark=LV_DL_4M limit-at=0 queue=LV_DL_4M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="LV_UL_3M" parent=public packet-mark=LV_UL_3M limit-at=0 queue=LV_UL_3M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="LV_UL_6M" parent=public packet-mark=LV_UL_6M limit-at=0 queue=LV_UL_6M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="OS_DL_1M" parent=local packet-mark=OS_DL_1M limit-at=0 queue=OS_DL_1M priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="OS_DL_256k" parent=local packet-mark=OS_DL_256k limit-at=0 queue=OS_DL_256k priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="OS_DL_512k" parent=local packet-mark=OS_DL_512k limit-at=0 queue=OS_DL_512k priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="OS_UL_128k" parent=public packet-mark=OS_UL_128k limit-at=0 queue=OS_UL_128k priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="OS_UL_256k" parent=public packet-mark=OS_UL_256k limit-at=0 queue=OS_UL_256k priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
add name="OS_UL_512k" parent=public packet-mark=OS_UL_512k limit-at=0 queue=OS_UL_512k priority=8 max-limit=0 burst-limit=0 \
burst-threshold=0 burst-time=0s disabled=no
3. Explanation
In /ip firewall address-list we created 3 lists for bandwitch profiles and list with name Latvia with latvian subnets In /ip firewall mangle we created address list based packet marks for bandwitch profiles. All ips witch is not included in any address list will have second bandwitch profiles rates. In /queue types we created pcq types for bandwitch profiles. In /queue tree we created rules with Local/Overseas packet marks and queue types for bandwitch profiles.
Now customer with ip 192।168.0.2 have 1 profile rates, customer with ip 192.168.0.3 have 2 profile rates, client with ip 192.168.0.4 have 3 profile rates and all others have 2 bandwitch rates, so all traffic will be limited and your cpu power will be free for other tasks.
source = http://wiki.mikrotik.com
How to apply different limits for Local/Overseas traffic
Introduction
Let's consider the scenario, when you want to apply different limit to Local and Oversea traffic. Oversea traffic - traffic that doesn't belong to the Local country traffic.
To distinguish oversea traffic from Local country traffic, we will use 'mangle marks' and 'address-list' features. It will place appropriate marks to the packets to/from the Local country and Oversea networks. Local traffic is 'latvian traffic' in the particular example, list of network numbers belonging to ISPs in Latvia can be extracted from file: http://www.nic.lv/local.net
Note, 'address-list' entries should be replaced with respective addresses, if your router isn't located in Latvia. To find the actual list of network numbers belonging to your country, use Google or any other resources.
Simple queues will limit data rate for the Local country traffic and Oversea traffic.
Quick Start for Impatient
Configuration export from the router:
/ ip firewall address-list
add list=Latvia address=159.148.0.0/16 comment="" disabled=no
add list=Latvia address=193.41.195.0/24 comment="" disabled=no
add list=Latvia address=193.41.33.0/24 comment="" disabled=no
add list=Latvia address=193.41.45.0/24 comment="" disabled=no
add list=Latvia address=193.68.64.0/19 comment="" disabled=no
add list=Latvia address=193.108.29.0/24 comment="" disabled=no
add list=Latvia address=193.108.144.0/22 comment="" disabled=no
add list=Latvia address=193.108.185.0/24 comment="" disabled=no
add list=Latvia address=193.109.211.0/24 comment="" disabled=no
add list=Latvia address=193.109.85.0/24 comment="" disabled=no
add list=Latvia address=193.110.8.0/23 comment="" disabled=no
add list=Latvia address=193.110.164.0/23 comment="" disabled=no
...
add list=Latvia address=193.111.244.0/22 comment="" disabled=no
/ ip firewall mangle
add chain=prerouting src-address=192.168.100.0/24 action=mark-connection \
new-connection-mark="Con Entire Traffic" passthrough=yes \
comment="Mark-connection All Traffic" disabled=no
add chain=prerouting src-address=192.168.100.0/24 connection-mark="Con Entire \
Traffic" dst-address-list=!Latvia action=mark-connection \
new-connection-mark="Con Oversea" passthrough=yes comment="Mark-connection \
Oversea Traffic" disabled=no
add chain=prerouting connection-mark="Con Oversea" action=mark-packet \
new-packet-mark="Oversea traffic" passthrough=no comment="Mark-packet \
Oversea Traffic" disabled=no
add chain=prerouting action=mark-packet new-packet-mark="Local Country Traffic" \
passthrough=no comment="Mark-packet Local Country Traffic" disabled=no
/ queue simple
add name="Oversea" target-addresses=192.168.100.254/32 dst-address=0.0.0.0/0 \
interface=all parent=none packet-marks="Oversea traffic" direction=both \
priority=8 queue=default-small/default-small limit-at=0/0 \
max-limit=256000/256000 total-queue=default-small disabled=no
add name="Local Country" target-addresses=192.168.100.254/32 dst-address=0.0.0.0/0 \
interface=all parent=none packet-marks="Local Country Traffic" direction=both \
priority=8 queue=default-small/default-small limit-at=0/0 \
max-limit=1024000/1024000 total-queue=default-small disabled=no
Explanation
Address-list
First we create Local country address-list, where are placed list of network numbers belonging to ISPs in Latvia (any other country network addresses can be used instead). Full address-list configuration is not included (too many address-list entries), but address-list idea is clear. Networks added to the list 'Latvia':
/ ip firewall address-list
add list=Latvia address=159.148.0.0/16 comment="" disabled=no
add list=Latvia address=193.41.195.0/24 comment="" disabled=no
add list=Latvia address=193.41.33.0/24 comment="" disabled=no
add list=Latvia address=193.41.45.0/24 comment="" disabled=no
add list=Latvia address=193.68.64.0/19 comment="" disabled=no
add list=Latvia address=193.108.29.0/24 comment="" disabled=no
add list=Latvia address=193.108.144.0/22 comment="" disabled=no
add list=Latvia address=193.108.185.0/24 comment="" disabled=no
add list=Latvia address=193.109.211.0/24 comment="" disabled=no
add list=Latvia address=193.109.85.0/24 comment="" disabled=no
add list=Latvia address=193.110.8.0/23 comment="" disabled=no
add list=Latvia address=193.110.164.0/23 comment="" disabled=no
...
add list=Latvia address=193.111.244.0/22 comment="" disabled=no
Note, it's much easier to create/edit such list with Excel or any other similar program.
Mangle
First we add rule to mark connections that belong to local router's subnet (192.168.100.0/24). Second rule marks connections between local subnet and overseas networks. Third rule marks oversea packets and exclude them from mangle table (passtrough=no). Finally, the last rule places packet mark on all packets that belong to Local country traffic.
/ ip firewall mangle
add chain=prerouting src-address=192.168.100.0/24 action=mark-connection \
new-connection-mark="Con Entire Traffic" passthrough=yes \
comment="Mark-connection All Traffic" disabled=no
add chain=prerouting src-address=192.168.100.0/24 connection-mark="Con Entire \
Traffic" dst-address-list=!Latvia action=mark-connection \
new-connection-mark="Con Oversea" passthrough=yes comment="Mark-connection \
Oversea Traffic" disabled=no
add chain=prerouting connection-mark="Con Oversea" action=mark-packet \
new-packet-mark="Oversea traffic" passthrough=no comment="Mark-packet \
Oversea Traffic" disabled=no
add chain=prerouting action=mark-packet new-packet-mark="Local Country Traffic" \
passthrough=no comment="Mark-packet Local Country Traffic" disabled=no
Simple Queue
Queue configuration is quite simple in the particular case. 192.168.100.254 is the local network host. First rule sets limit 256k/256k to Oversea traffic for the particular host. Respectively second simple queue set limit 1M/1M for Local country traffic.
/ queue simple
add name="Oversea" target-addresses=192.168.100.254/32 dst-address=0.0.0.0/0 \
interface=all parent=none packet-marks="Oversea traffic" direction=both \
priority=8 queue=default-small/default-small limit-at=0/0 \
max-limit=256000/256000 total-queue=default-small disabled=no
add name="Local Country" target-addresses=192.168.100.254/32 dst-address=0.0.0.0/0 \
interface=all parent=none packet-marks="Local Country Traffic" direction=both \
priority=8 queue=default-small/default-small limit-at=0/0 \
max-limit=1024000/1024000 total-queue=default-small disabled=no
Per-Traffic Load Balancing
Introduction
Bandwidth management is an essential part of everyday operation for typcial ISPs, businesses, and even everday home users. There are many different types of management tools available to RouterOS users, QOS, rate-limiting, packet-limiting, to name a few.
I personally operate a wireless ISP, in an area that has no other type of convential high-speed internet (ie. cable, fibre, or DSL). Not having access to fibre myself, I am in a situation where the single fastest backbone connection I can get does not provide enough bandwidth for me to have only one connection. As a result of this limitation load-balancing multiple internet backbone connections is very important.
In the past I have used ECMP, persistent per connection styled load-balancing (see http://wiki.mikrotik.com/wiki/Load_Balancing), as well as various other methods. However, I found all of them lacking in various different areas (not load-balancing correctly, broken large HTTP downloads, IM problems, to name a few issues). I then investigated a way to give me more control over my bandwidth while minimizing the potential problems. The end result was a per-traffic type of load-balancing. This tutorial is designed address that one specific area in depth, at a later date, I may expand/add additional info on fail-over, QOS, and other topics.
Functions of RouterOS Used
Main functions of RouterOS used in this tutorial
- Firewall mangle rules
- Firewall address-lists
- Routing
Step 1 - How to break up to traffic
Before you even log onto your RouterOS box, you should have an idea of how you want to divide your traffic, and have an understanding of what traffic can and what traffic can't be broken up.
Here is an example of what you may want to attempt to seperate (in no particular order):
- HTTP traffic (port 80)
- SSL traffic (port 443)
- POP3 traffic (port 110)
- SMTP traffic (port 25)
- P2P traffic (various ports)
- Unknown traffic (various ports)
After making a list of the traffic type, and the ports they operate on, you need to look at the list and decide if it is at all even capable of being forced out a certain internet connection.
Using the above list as an example here is what I came up with:
- HTTP traffic (no problems found yet)
- SSL traffic (some issues, for normal SSL websites and 90% of all software it is not a problem, I'll explain why issues can arise later)
- POP3 traffic (no problems found yet)
- SMTP traffic (no problems found yet)
- P2P traffic (must go out same internet connection as Unknown traffic, I'll explain why this is later)
- Unknown traffic (must go out same internet connection as P2P traffic, I'll explain why this is later)
Now for a quick explanation of why there can be some issues depending on the traffic type. Some website/programs do not play friendly with multiple requests from different IP addresses, this is the reason why ECMP has so many problems. I will provide a simple solution to the rare conditions where load-balancing can't be completed.
Again using the above as an example lets explain where and why issues can arise. SSL - The beauty of a website is that there are seperate requests for different data, ie. loading pictures from 3 different sources would be a request to each respective server. The result is if a we have a website that uses both SSL and HTTP traffic, we know that in most cases the website will just answer the request without care of the originating IP address. However, and this is a special case, if the website/program developer checks where the requests are originating and they find that the IPs are different they may not successfully answer those requests (this can be by design or by accident). I have had 2 cases of this, in both casees it was secured medical websites that were using it as a method of protecting their data.
P2P and Unknown - I am addressing these together because the issue is one and the same. RouterOS doesn't identify P2P based on any single condition, but instead analyzes the packets, this means RouterOS needs time to watch the data before it realizes that is in fact P2P traffic. As a result RouterOS doesn't know the data is P2P until AFTER the connection is made. This is important becuase the only way to send data out a specific internet connection you must know what that traffic is BEFORE the connection is made. So as with P2P traffic, unknown traffic is just that, it is unknown. By marking the unknown traffic though you can control what internet connection is used for both P2P and the left over unknown traffic (very useful).
Step 2 - Setting up the network
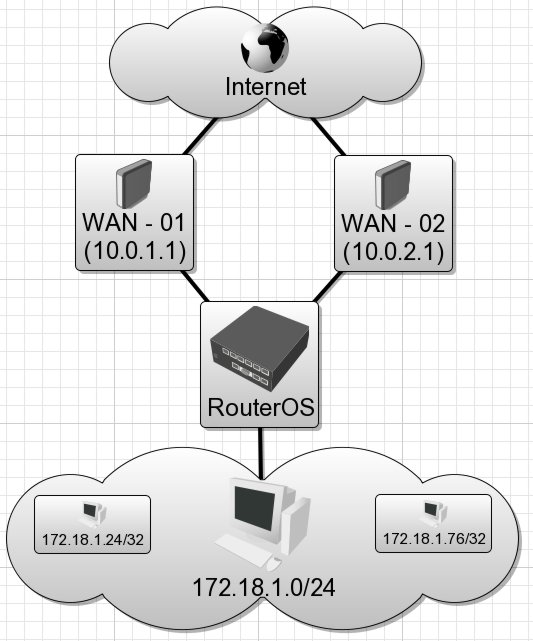
Before we get to the real point of this tutorial we need a fictious network we can use as an example.
- Client Computers (172.18.1.0/24)
- Internet Gateways (10.0.1.1/24, 10 0.2.1/24)
- RouterOS IPs (10.0.1.2/24, 10.0.2.2/24)
Assuming that the IPs, default routes, and DNS settings are already in place the following allows users to get internet access.
Create Address-List for permitted use of internet
/ ip firewall address-list
add list="Allowed - Internet" address=172.18.1.0/24 comment="" disabled=no
Create Address-List to bypass load-balancing
/ ip firewall address-list
add list="WAN - 01" address=172.18.1.24/32 comment="" disabled=no
add list="WAN - 02" address=172.18.1.76/32 comment="" disabled=no
Apply 'Masquerading' to the traffic leaving the WAN interfaces
/ ip firewall nat
add chain=srcnat action=masquerade out-interface="WAN - 01" src-address-list="Allowed - Internet" comment="Gateway 10.0.1.1/24" disabled=no
add chain=srcnat action=masquerade out-interface="WAN - 02" src-address-list="Allowed - Internet" comment="Gateway 10.0.2.1/24" disabled=no
Clients should be able to browse the internet, however only one internet connection would be used (the current default route in RouterOS)
Step 3 - Using RouterOS's Mangle tool to mark specific traffic
This following is the necessary RouterOS commands to mark particular traffic for a certain route, we are using the same example for traffic types as in the beginning, HTTP, SSL, POP3, SMTP, P2P, and Uknown
/ ip firewall mangle
add chain=prerouting action=mark-routing new-routing-mark="WAN - 01" src-address-list="WAN - 01" passthrough=no comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="WAN - 02" src-address-list="WAN - 02" passthrough=no comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="HTTP Traffic" passthrough=no dst-port=80 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="SSL Traffic" passthrough=no dst-port=443 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="POP3 Traffic" passthrough=no dst-port=110 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="SMTP Traffic" passthrough=no dst-port=25 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="P2P Traffic" passthrough=no p2p=all-p2p comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="Unknown Traffic" passthrough=no comment="" disabled=no
The first two lines provide a method of marking particular clients to bypass the load-balancing and use only a certain internet connection for all of their traffic. The following lines with mark traffic based on the the dst-port, notice how we are not passing though, also notice that we are marking all traffic, even if its not known, this always for a different internet connection to be specified for the Unknown and P2P instead of using the router's defult route. I also mark P2P seperately even though it must go out the same internet connection as Unknown traffic, I do this for a couple reasons, one is that I could easily stop all P2P traffic by disabling a route, and the other is in my RouterOS configuration I use alot of QOS, it it very easy to remember how everything is configured if the QOS mirrors the load-balancing.
So now we are marking traffic for their respective routes, next is to add those actual routes.
[edit] Step 4 - Using the Routing fuctions of RouterOS to force traffic out certain internet connections
This following is the necessary RouterOS commands to provide routes for the marked HTTP, SSL, POP3, SMTP, P2P, and Uknown Traffic
/ ip route
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="WAN - 01" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="WAN - 02" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="HTTP Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="SSL Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="POP3 Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="SMTP Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="P2P Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="Unknown Traffic" comment="" disabled=no
The first two line provide the routes necessary to give the clients that are not being load-balanced via traffic type the correct gateway to the internet. The remaining lines are the routes necessary to provide the appropiate gateway based on traffic type.
Step 5 - Review what you've created
What did you do:
- You intelligently broke up your internet traffic into different types
- You marked that traffic using the Mangle tool of RouterOS
- You created a bypass list to allow certain IP to bypass the Per-Traffic Load Balancing
- You assigned particular routes based on the traffic you marked with Mangle
[edit] Conclusion
What you have have done is very powerful and this tutorial provides just the tip of the iceberg so to say. The traffic types I have listed here are only a small amount of the total and you may want to add others (eg. DNS, terminal services, ICMP, etc). This can be used is a great deal of different ways be it in a small office enviroment (seperating your email usage from your browsing) or a large wireless ISP (for load-balancing). Some tips and final thoughts:
- Think though what you want to achieve before you start
- Pay attention to the type of traffic on each line (is it incoming intensive or outgoing intensive)
- Finally experiment, nothing better then finding better, faster and more intelligent ways to improve your services with little capital costs
Per-Traffic Load Balancing
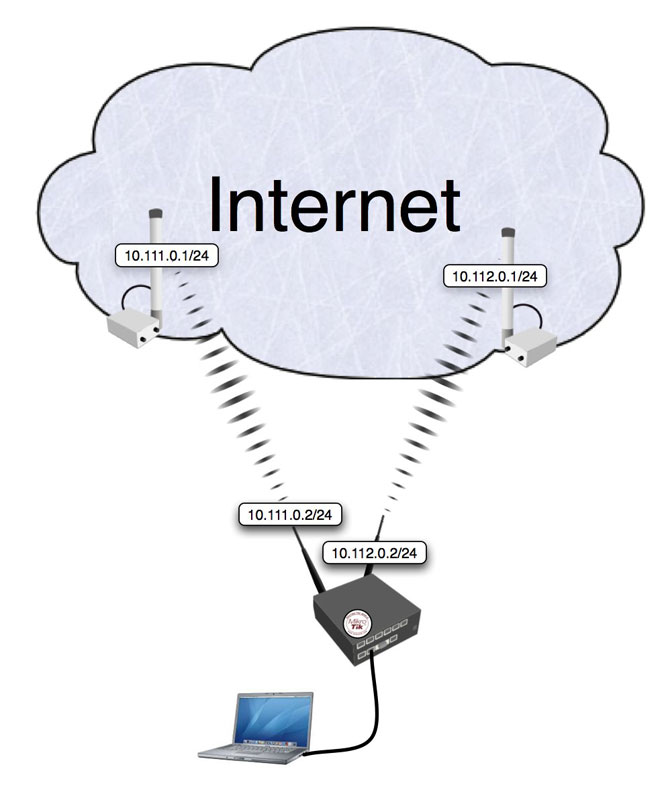
Introduction
Bandwidth management is an essential part of everyday operation for typcial ISPs, businesses, and even everday home users. There are many different types of management tools available to RouterOS users, QOS, rate-limiting, packet-limiting, to name a few.
I personally operate a wireless ISP, in an area that has no other type of convential high-speed internet (ie. cable, fibre, or DSL). Not having access to fibre myself, I am in a situation where the single fastest backbone connection I can get does not provide enough bandwidth for me to have only one connection. As a result of this limitation load-balancing multiple internet backbone connections is very important.
In the past I have used ECMP, persistent per connection styled load-balancing (see http://wiki.mikrotik.com/wiki/Load_Balancing), as well as various other methods. However, I found all of them lacking in various different areas (not load-balancing correctly, broken large HTTP downloads, IM problems, to name a few issues). I then investigated a way to give me more control over my bandwidth while minimizing the potential problems. The end result was a per-traffic type of load-balancing. This tutorial is designed address that one specific area in depth, at a later date, I may expand/add additional info on fail-over, QOS, and other topics.
Functions of RouterOS Used
Main functions of RouterOS used in this tutorial
- Firewall mangle rules
- Firewall address-lists
- Routing
Step 1 - How to break up to traffic
Before you even log onto your RouterOS box, you should have an idea of how you want to divide your traffic, and have an understanding of what traffic can and what traffic can't be broken up.
Here is an example of what you may want to attempt to seperate (in no particular order):
- HTTP traffic (port 80)
- SSL traffic (port 443)
- POP3 traffic (port 110)
- SMTP traffic (port 25)
- P2P traffic (various ports)
- Unknown traffic (various ports)
After making a list of the traffic type, and the ports they operate on, you need to look at the list and decide if it is at all even capable of being forced out a certain internet connection.
Using the above list as an example here is what I came up with:
- HTTP traffic (no problems found yet)
- SSL traffic (some issues, for normal SSL websites and 90% of all software it is not a problem, I'll explain why issues can arise later)
- POP3 traffic (no problems found yet)
- SMTP traffic (no problems found yet)
- P2P traffic (must go out same internet connection as Unknown traffic, I'll explain why this is later)
- Unknown traffic (must go out same internet connection as P2P traffic, I'll explain why this is later)
Now for a quick explanation of why there can be some issues depending on the traffic type. Some website/programs do not play friendly with multiple requests from different IP addresses, this is the reason why ECMP has so many problems. I will provide a simple solution to the rare conditions where load-balancing can't be completed.
Again using the above as an example lets explain where and why issues can arise. SSL - The beauty of a website is that there are seperate requests for different data, ie. loading pictures from 3 different sources would be a request to each respective server. The result is if a we have a website that uses both SSL and HTTP traffic, we know that in most cases the website will just answer the request without care of the originating IP address. However, and this is a special case, if the website/program developer checks where the requests are originating and they find that the IPs are different they may not successfully answer those requests (this can be by design or by accident). I have had 2 cases of this, in both casees it was secured medical websites that were using it as a method of protecting their data.
P2P and Unknown - I am addressing these together because the issue is one and the same. RouterOS doesn't identify P2P based on any single condition, but instead analyzes the packets, this means RouterOS needs time to watch the data before it realizes that is in fact P2P traffic. As a result RouterOS doesn't know the data is P2P until AFTER the connection is made. This is important becuase the only way to send data out a specific internet connection you must know what that traffic is BEFORE the connection is made. So as with P2P traffic, unknown traffic is just that, it is unknown. By marking the unknown traffic though you can control what internet connection is used for both P2P and the left over unknown traffic (very useful).
Step 2 - Setting up the network
Before we get to the real point of this tutorial we need a fictious network we can use as an example.
- Client Computers (172.18.1.0/24)
- Internet Gateways (10.0.1.1/24, 10 0.2.1/24)
- RouterOS IPs (10.0.1.2/24, 10.0.2.2/24)
Assuming that the IPs, default routes, and DNS settings are already in place the following allows users to get internet access.
Create Address-List for permitted use of internet
/ ip firewall address-list
add list="Allowed - Internet" address=172.18.1.0/24 comment="" disabled=no
Create Address-List to bypass load-balancing
/ ip firewall address-list
add list="WAN - 01" address=172.18.1.24/32 comment="" disabled=no
add list="WAN - 02" address=172.18.1.76/32 comment="" disabled=no
Apply 'Masquerading' to the traffic leaving the WAN interfaces
/ ip firewall nat
add chain=srcnat action=masquerade out-interface="WAN - 01" src-address-list="Allowed - Internet" comment="Gateway 10.0.1.1/24" disabled=no
add chain=srcnat action=masquerade out-interface="WAN - 02" src-address-list="Allowed - Internet" comment="Gateway 10.0.2.1/24" disabled=no
Clients should be able to browse the internet, however only one internet connection would be used (the current default route in RouterOS)
Step 3 - Using RouterOS's Mangle tool to mark specific traffic
This following is the necessary RouterOS commands to mark particular traffic for a certain route, we are using the same example for traffic types as in the beginning, HTTP, SSL, POP3, SMTP, P2P, and Uknown
/ ip firewall mangle
add chain=prerouting action=mark-routing new-routing-mark="WAN - 01" src-address-list="WAN - 01" passthrough=no comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="WAN - 02" src-address-list="WAN - 02" passthrough=no comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="HTTP Traffic" passthrough=no dst-port=80 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="SSL Traffic" passthrough=no dst-port=443 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="POP3 Traffic" passthrough=no dst-port=110 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="SMTP Traffic" passthrough=no dst-port=25 protocol=tcp comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="P2P Traffic" passthrough=no p2p=all-p2p comment="" disabled=no
add chain=prerouting action=mark-routing new-routing-mark="Unknown Traffic" passthrough=no comment="" disabled=no
The first two lines provide a method of marking particular clients to bypass the load-balancing and use only a certain internet connection for all of their traffic. The following lines with mark traffic based on the the dst-port, notice how we are not passing though, also notice that we are marking all traffic, even if its not known, this always for a different internet connection to be specified for the Unknown and P2P instead of using the router's defult route. I also mark P2P seperately even though it must go out the same internet connection as Unknown traffic, I do this for a couple reasons, one is that I could easily stop all P2P traffic by disabling a route, and the other is in my RouterOS configuration I use alot of QOS, it it very easy to remember how everything is configured if the QOS mirrors the load-balancing.
So now we are marking traffic for their respective routes, next is to add those actual routes.
Step 4 - Using the Routing fuctions of RouterOS to force traffic out certain internet connections
This following is the necessary RouterOS commands to provide routes for the marked HTTP, SSL, POP3, SMTP, P2P, and Uknown Traffic
/ ip route
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="WAN - 01" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="WAN - 02" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="HTTP Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="SSL Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.2.1 scope=255 target-scope=10 routing-mark="POP3 Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="SMTP Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="P2P Traffic" comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.0.1.1 scope=255 target-scope=10 routing-mark="Unknown Traffic" comment="" disabled=no
The first two line provide the routes necessary to give the clients that are not being load-balanced via traffic type the correct gateway to the internet. The remaining lines are the routes necessary to provide the appropiate gateway based on traffic type.
Step 5 - Review what you've created
What did you do:
- You intelligently broke up your internet traffic into different types
- You marked that traffic using the Mangle tool of RouterOS
- You created a bypass list to allow certain IP to bypass the Per-Traffic Load Balancing
- You assigned particular routes based on the traffic you marked with Mangle
Conclusion
What you have have done is very powerful and this tutorial provides just the tip of the iceberg so to say. The traffic types I have listed here are only a small amount of the total and you may want to add others (eg. DNS, terminal services, ICMP, etc). This can be used is a great deal of different ways be it in a small office enviroment (seperating your email usage from your browsing) or a large wireless ISP (for load-balancing). Some tips and final thoughts:
- Think though what you want to achieve before you start
- Pay attention to the type of traffic on each line (is it incoming intensive or outgoing intensive)
- Finally experiment, nothing better then finding better, faster and more intelligent ways to improve your services with little capital costs
Load Balancing
With NAT and policy routing, with working HTTPS, IM and large downloads
Consider the following network layout:
Quick Start for Impatient
Configuration export from the gateway router:
/ ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local comment="" \
disabled=no
add address=10.111.0.2/24 network=10.111.0.0 broadcast=10.111.0.255 interface=wlan2 \
comment="" disabled=no
add address=10.112.0.2/24 network=10.112.0.0 broadcast=10.112.0.255 interface=wlan1 \
comment="" disabled=no
/ ip firewall mangle
add chain=prerouting in-interface=Local connection-state=new nth=1,1,0 \
action=mark-connection new-connection-mark=odd passthrough=yes comment="" \
disabled=no
add chain=prerouting in-interface=Local connection-mark=odd action=mark-routing \
new-routing-mark=odd passthrough=no comment="" disabled=no
add chain=prerouting in-interface=Local connection-state=new nth=1,1,1 \
action=mark-connection new-connection-mark=even passthrough=yes comment="" \
disabled=no
add chain=prerouting in-interface=Local connection-mark=even action=mark-routing \
new-routing-mark=even passthrough=no comment="" disabled=no
/ ip firewall nat
add chain=srcnat connection-mark=odd action=src-nat to-addresses=10.111.0.2 \
to-ports=0-65535 comment="" disabled=no
add chain=srcnat connection-mark=even action=src-nat to-addresses=10.112.0.2 \
to-ports=0-65535 comment="" disabled=no
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1 scope=255 target-scope=10 routing-mark=odd \
comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.112.0.1 scope=255 target-scope=10 routing-mark=even \
comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.112.0.1 scope=255 target-scope=10 comment="" \
disabled=no
Explanation
First we give a code snippet and then explain what it actually does.
Mangle
/ ip address
add address=192.168.0.1/24 network=192.168.0.0 broadcast=192.168.0.255 interface=Local comment="" \
disabled=no
add address=10.111.0.2/24 network=10.111.0.0 broadcast=10.111.0.255 interface=wlan2 \
comment="" disabled=no
add address=10.112.0.2/24 network=10.112.0.0 broadcast=10.112.0.255 interface=wlan1 \
comment="" disabled=no
The router has two upstream (WAN) interfaces with the addresses of 10.111.0.2/24 and 10.112.0.2/24. The LAN interface has the name "Local" and IP address of 192.168.0.1/24.
/ ip firewall mangle
add chain=prerouting in-interface=Local connection-state=new nth=1,1,0 \
action=mark-connection new-connection-mark=odd passthrough=yes comment="" \
disabled=no
First we take every second packet that establishes new session (note connection-state=new), and mark it with connection mark "odd". Consequently all successive packets belonging to the same session will carry the connection mark "odd". Note that we are passing these packets to the second rule (passthrough=yes) to place a routing mark on these packets in addition to the connection mark.
add chain=prerouting in-interface=Local connection-mark=odd action=mark-routing \
new-routing-mark=odd passthrough=no comment="" disabled=no
The rule above places the routing mark "odd" on all packets that belong to the "odd" connection and stops processing all other mangle in prerouting chain rules for these packets.
add chain=prerouting in-interface=Local connection-state=new nth=1,1,1 \
action=mark-connection new-connection-mark=even passthrough=yes comment="" \
disabled=no
add chain=prerouting in-interface=Local connection-mark=even action=mark-routing \
new-routing-mark=even passthrough=no comment="" disabled=no
These rules do the same for the remaining half of the traffic as the first two rules for the first half of the traffic.
The code above effectively means that each new connection initiated through the router from the local network will be marked as either "odd" or "even" with both routing and connection marks.
NAT
/ ip firewall nat
add chain=srcnat connection-mark=odd action=src-nat to-addresses=10.111.0.2 \
to-ports=0-65535 comment="" disabled=no
add chain=srcnat connection-mark=even action=src-nat to-addresses=10.112.0.2 \
to-ports=0-65535 comment="" disabled=no
All traffic marked "odd" is being NATted to source IP address of 10.111.0.2, while traffic marked "even" gets "10.112.0.2" source IP address.
Routing
/ ip route
add dst-address=0.0.0.0/0 gateway=10.111.0.1 scope=255 target-scope=10 routing-mark=odd \
comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.112.0.1 scope=255 target-scope=10 routing-mark=even \
comment="" disabled=no
add dst-address=0.0.0.0/0 gateway=10.112.0.1 scope=255 target-scope=10 comment="" \
disabled=no comment="gateway for the router itself"
For all traffic marked "odd" (consequently having 10।111.0.2 translated source address) we use 10.111.0.1 gateway. In the same manner all traffic marked "even" is routed through the 10.112.0.1 gateway. Finally, we have one additional entry specifying that traffic from the router itself (the traffic without any routing marks) should go to 10.112.0.1 gateway.
सोर्स = ह्त्त्प://विकी.मिक्रोतिक.कॉम